Threat intelligence enriched with External Attack Surface Management, Brand Protection, and Dark Web Radar.
Protect your business from the dangers lurking in the hidden corners of the internet.
Effective threat hunting and threat actor tracking with behavioral analytics.
Discover your assets with a hacker mindset.
Stay ahead of threat actors with actionable intelligence alerts.
Evaluate the security posture of your entire supply network.
Your guide in harnessing the full potential of our platform.
Hear SOCRadar’s impressive achievements from our clients.
Automate and operationalize your security operations.
Consulting and professional services for cybersecurity excellence.
Industry, sector, and region-based in-depth research.
Discover the heartbeat of cyberspace through a collection showcasing the latest incidents.
Discover how XTI empowers organizations to proactively identify, mitigate, and respond to evolving cyber threats.
Register for our live webinars, and watch our on-demand webinars instantly.
Dive deep into the world of cyber threats, advanced analysis techniques, and cutting-edge strategies.
Stay informed and up-to-date on the latest cybersecurity trends.
Explore SOCRadar’s learning experience to fuel your cybersecurity journey with insights that exceed industry standards.
We offer expert-led, and exclusive trainings to help you master the latest in cybersecurity, trusted by over 2,000 top companies.
Scan the dark web to prevent your leaks from turning into real risks.
Instantly access dark web findings about your organization’s assets.
Check if there is anything about you in SOCRadar’s ever-expanding breach database.
Track threat actors and groups by country or industry for effective follow-up.
Explore threat actors’ tactics, techniques, activities, and detailed profiles targeting your industry or region.
All-in-one next-generation tools for investigating everyday events like phishing, malware, account breach, etc.
Power your search with SOCRadar’s IOC Radar.
Let’s get to know each other better.
Broaden your market reach and increase ARR with SOCRadar Extended Threat Intelligence.
Get informed of our upcoming events.
Latest news about our platform, company, and what’s being said about us.
Begin an extraordinary journey in your professional path with SOCRadar.
We’d like to hear from you.
SOCRadar Training Series – Mastering AI in Cybersecurity From Theory to Practice
Resources
On April 3, 2024, a newly discovered ransomware group surfaced as Senior Threat Analyst Rakesh Krishnan shed light. Known as Red CryptoApp, this group began its operations between February and March, coinciding with the dismantling or retreat of Lockbit and ALPHV.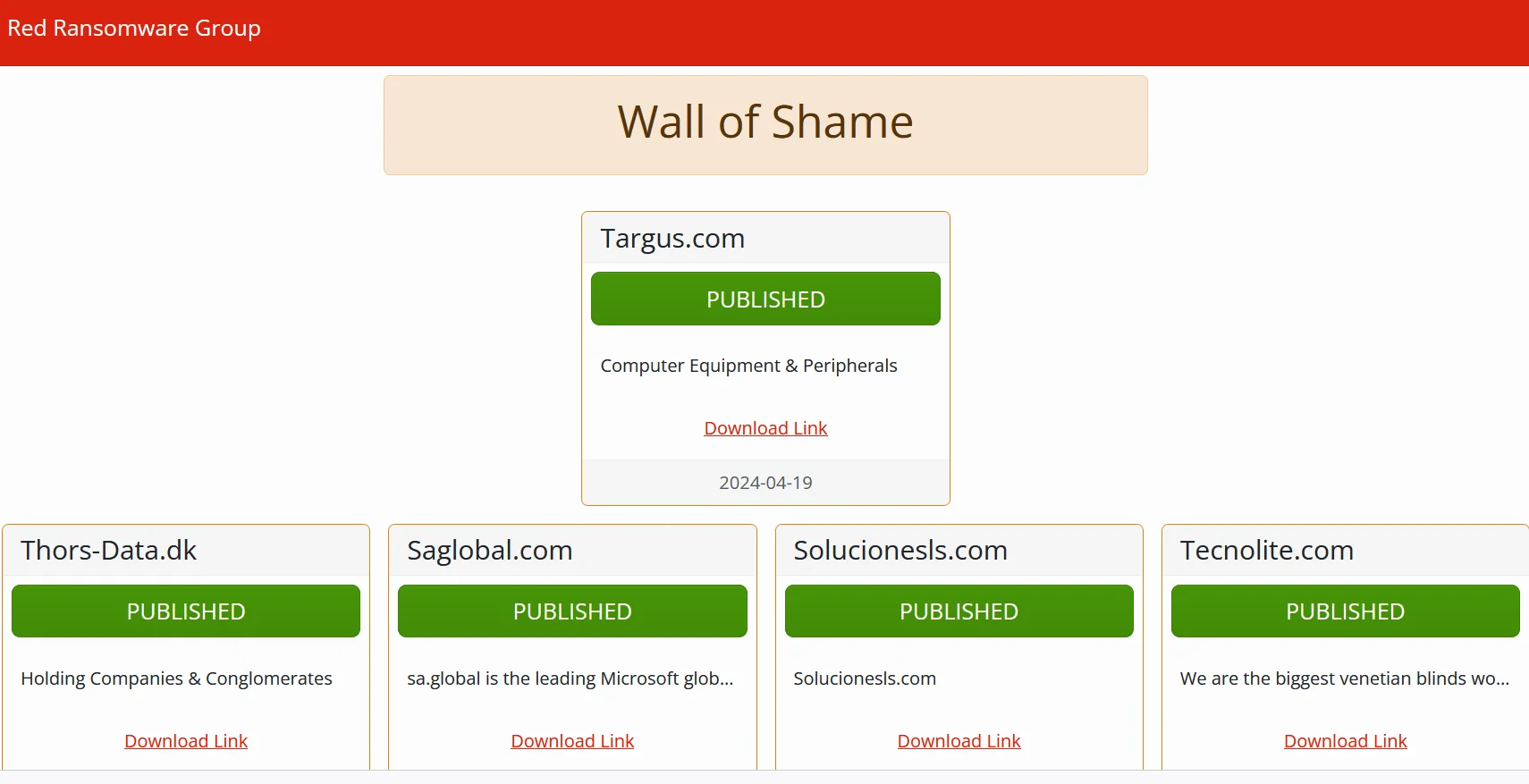
Red Ransomware Group’s Wall of Shame
Red Ransomware or Red CryptoApp, a fresh ransomware group, surfaced in March 2024 and promptly revealed the data of 11 victims on its Data Leak Site (DLS), along with announcing an additional victim.
Their DLS debuted on March 29, 2024, titled “Wall of Shame.” Interestingly, the group chose to release the data of all 11 victims simultaneously on March 5, 2024, indicating a strategic delay in publishing the information. This tactic hints that Red CryptoApp probably have initiated their activities earlier and deliberately held off on disclosing the data for a greater effect.
The victimology report for Red Ransomware reveals a narrow range of targets across a few sectors and countries. The majority of victims, mainly in the United States, represent industries such as Information Technology, Legal, Hospitality, Transportation, Manufacturing, Education, Electronics, and Retail.
This narrow targeting could indicate Red Ransomware’s focused approach, possibly because of lack of wide capabilities. The overview also notes a recent victim in the Retail sector from the United States, indicating that the group’s activities extend beyond its initial incident on March 5, 2024, showcasing ongoing threats posed by Red Ransomware.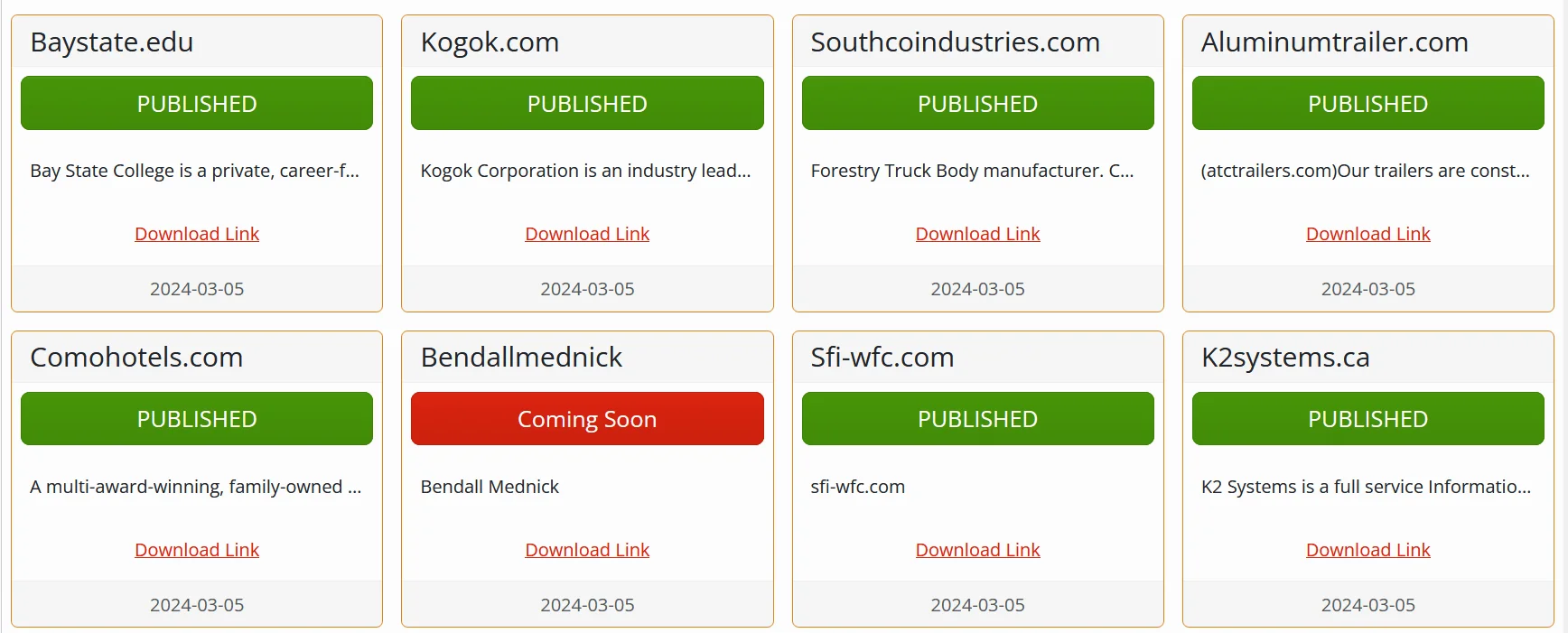
Wall of Shame – 2
The inclusion of victims from Canada, Singapore, Mexico, Spain, Italy, India and Denmark shows the narrow international reach of the Red Ransomware group. Most Western affiliated countries and heavy targeting US, also show a classical ransomware approach.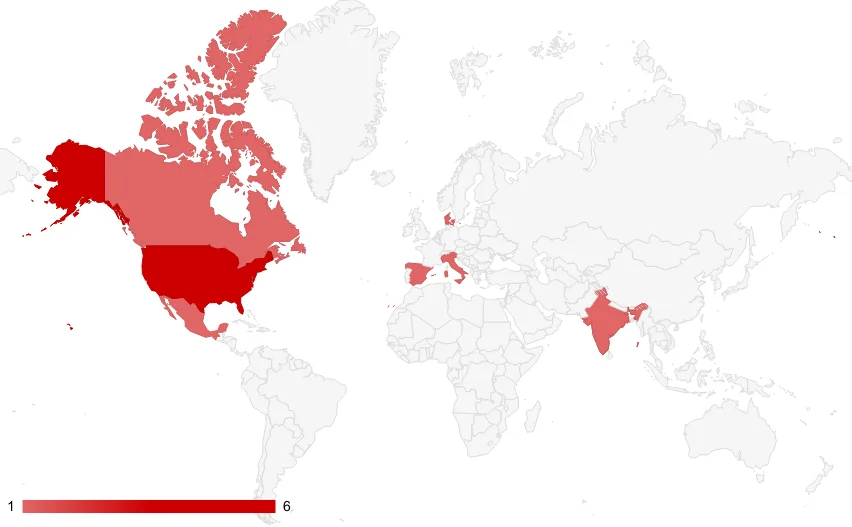
Targeted countries, most targets were US based
There isn’t detailed incident analysis for public research other than Rakesh Krishnan at Netenrich shared. The known facts are detailed below:
Infection Method:
Red Ransomware infects systems by exploiting vulnerabilities or using phishing emails with malicious attachments. Once a system is compromised, all files are modified with the .REDCryptoApp extension, rendering them inaccessible.
Target Selection:
Victim Interaction:
Victim contact interface (Medium)
Use of AI Tools:
Global Impact:
Red Ransomware group featured Targus on its dark leak site “Wall of Shame,” displaying a red “Coming Soon” banner beneath the company’s name in early April and now its data has allegedly been published.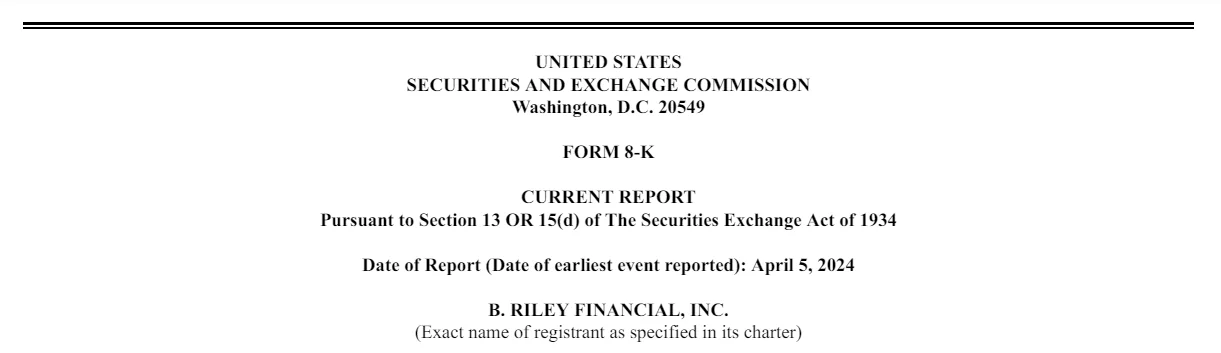
SEC Filing by the company
On April 8th, Targus’ parent company, B. Riley Financial, submitted an 8K breach disclosure to the US Securities and Exchange Commission (SEC). The Los Angeles-based financial investment firm, which acquired Targus in October 2022, revealed that an unauthorized threat actor gained access to certain file systems on April 5th.
Upon detection, Targus promptly shut down its systems to mitigate damage and isolate the attacker. B. Riley noted in the SEC disclosure that while this action temporarily disrupted business operations, external experts were already engaged in restoring the compromised systems.
The filing did not specify whether B. Riley was aware of the identity of the attackers or the duration of their presence within the network. Furthermore, details regarding the affected systems or the extent of data compromise were not disclosed in the filing.
But it has definitively shown that this small-scale and seemingly not very sophisticated group can cause real harm.
Red Ransomware’s modus operandi encompasses somewhat regular infection methods, narrow industry targeting and international operation. The integration of AI tools in victim interactions and combination of regular tactics underscores the group’s novice capabilities but still highlights the ongoing threat posed by ransomware groups in the cybersecurity landscape.
SOCRadar offers a robust defense strategy tailored to counter the ransomware threat. Our proactive approach to threat monitoring and intelligence solutions is crafted to enhance your organization’s security posture effectively. Using our platform, you can actively monitor and analyze threat actors, gaining comprehensive insights into their tactics, targeted vulnerabilities, affiliations, and indicators of compromise. This proactive methodology enables you to anticipate and mitigate potential threats efficiently, safeguarding your critical assets.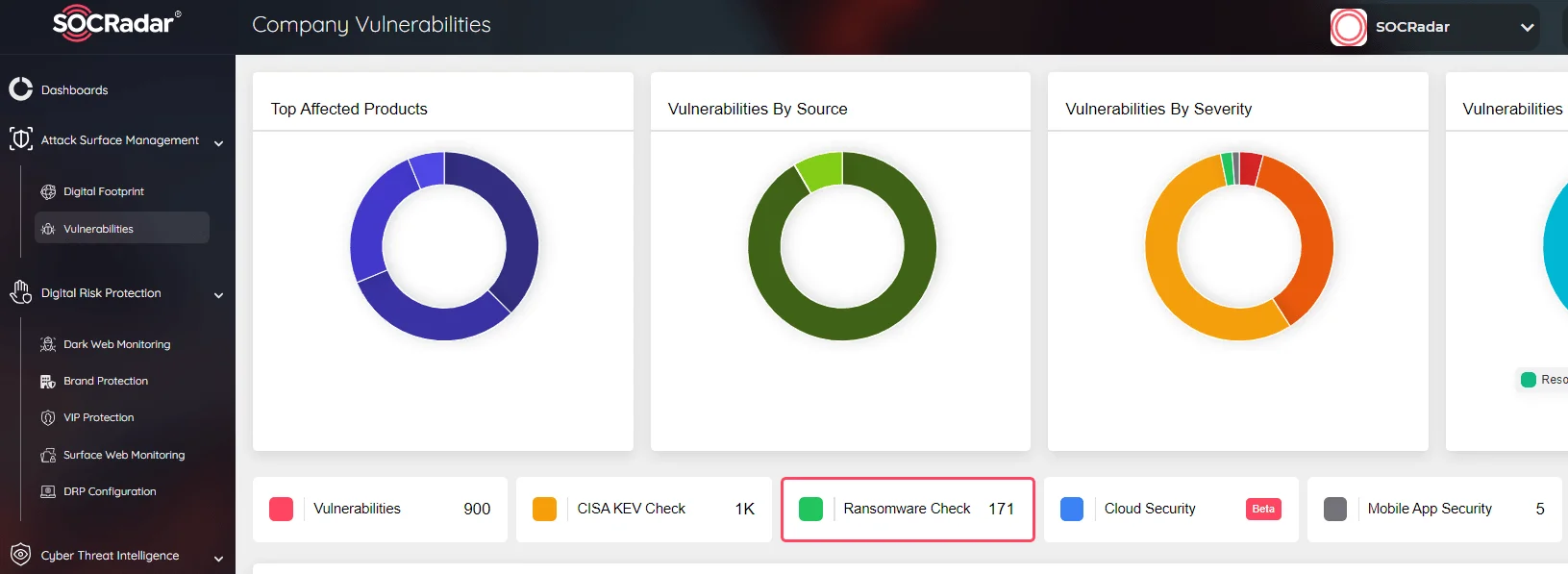
SOCRadar Company Vulnerabilities, Ransomware Check
Moreover, our Attack Surface Management module, incorporating the Ransomware Check function, ensures continuous monitoring of all potential attack vectors. This guarantees real-time alerts regarding any suspicious activities related to ransomware. By staying ahead of these threats, you can swiftly respond and fortify your cybersecurity defenses, minimizing the risk posed by emerging threats.
Subscribe to our newsletter and stay updated on the latest insights!
PROTECTION OF PERSONAL DATA COOKIE POLICY FOR THE INTERNET SITE
Protecting your personal data is one of the core principles of our organization, SOCRadar, which operates the internet site (www.socradar.com). This Cookie Usage Policy (“Policy”) explains the types of cookies used and the conditions under which they are used to all website visitors and users.
Cookies are small text files stored on your computer or mobile device by the websites you visit.
Cookies are commonly used to provide you with a personalized experience while using a website, enhance the services offered, and improve your overall browsing experience, contributing to ease of use while navigating a website. If you prefer not to use cookies, you can delete or block them through your browser settings. However, please be aware that this may affect your usage of our website. Unless you change your cookie settings in your browser, we will assume that you accept the use of cookies on this site.
1. WHAT KIND OF DATA IS PROCESSED IN COOKIES?
Cookies on websites collect data related to your browsing and usage preferences on the device you use to visit the site, depending on their type. This data includes information about the pages you access, the services and products you explore, your preferred language choice, and other preferences.
2. WHAT ARE COOKIES AND WHAT ARE THEIR PURPOSES?
Cookies are small text files stored on your device or web server by the websites you visit through your browsers. These small text files, containing your preferred language and other settings, help us remember your preferences on your next visit and assist us in making improvements to our services to enhance your experience on the site. This way, you can have a better and more personalized user experience on your next visit.
The main purposes of using cookies on our Internet Site are as follows:
3. TYPES OF COOKIES USED ON OUR INTERNET SITE 3.1. Session Cookies
Session cookies ensure the smooth operation of the internet site during your visit. They are used for purposes such as ensuring the security and continuity of our sites and your visits. Session cookies are temporary cookies and are deleted when you close your browser; they are not permanent.
3.2. Persistent Cookies
These cookies are used to remember your preferences and are stored on your device through browsers. Persistent cookies remain stored on your device even after you close your browser or restart your computer. These cookies are stored in your browser’s subfolders until deleted from your browser’s settings. Some types of persistent cookies can be used to provide personalized recommendations based on your usage purposes.
With persistent cookies, when you revisit our website with the same device, the website checks if a cookie created by our website exists on your device. If so, it is understood that you have visited the site before, and the content to be presented to you is determined accordingly, offering you a better service.
3.3. Mandatory/Technical Cookies
Mandatory cookies are essential for the proper functioning of the visited internet site. The purpose of these cookies is to provide necessary services by ensuring the operation of the site. For example, they allow access to secure sections of the internet site, use of its features, and navigation.
3.4. Analytical Cookies
These cookies gather information about how the website is used, the frequency and number of visits, and show how visitors navigate to the site. The purpose of using these cookies is to improve the operation of the site, increase its performance, and determine general trend directions. They do not contain data that can identify visitors. For example, they show the number of error messages displayed or the most visited pages.
3.5. Functional Cookies
Functional cookies remember the choices made by visitors within the site and recall them during the next visit. The purpose of these cookies is to provide ease of use to visitors. For example, they prevent the need to re-enter the user’s password on each page visited by the site user.
3.6. Targeting/Advertising Cookies
They measure the effectiveness of advertisements shown to visitors and calculate how many times ads are displayed. The purpose of these cookies is to present personalized advertisements to visitors based on their interests.
Similarly, they determine the specific interests of visitors’ navigation and present appropriate content. For example, they prevent the same advertisement from being shown again to the visitor in a short period.
4. HOW TO MANAGE COOKIE PREFERENCES?
To change your preferences regarding the use of cookies, block or delete cookies, you only need to change your browser settings.
Many browsers offer options to accept or reject cookies, only accept certain types of cookies, or receive notifications from the browser when a website requests to store cookies on your device.
Also, it is possible to delete previously saved cookies from your browser.
If you disable or reject cookies, you may need to manually adjust some preferences, and certain features and services on the website may not work properly as we will not be able to recognize and associate with your account. You can change your browser settings by clicking on the relevant link from the table below.
5. EFFECTIVE DATE OF THE INTERNET SITE PRIVACY POLICY
The Internet Site Privacy Policy is dated The effective date of the Policy will be updated if the entire Policy or specific sections are renewed. The Privacy Policy is published on the Organization’s website (www.socradar.com) and made accessible to relevant individuals upon request.
SOCRadar
Address: 651 N Broad St, Suite 205 Middletown, DE 19709 USA
Phone: +1 (571) 249-4598
Email: [email protected]
Website: www.socradar.com
