Threat intelligence enriched with External Attack Surface Management, Brand Protection, and Dark Web Radar.
Protect your business from the dangers lurking in the hidden corners of the internet.
Effective threat hunting and threat actor tracking with behavioral analytics.
Discover your assets with a hacker mindset.
Stay ahead of threat actors with actionable intelligence alerts.
Evaluate the security posture of your entire supply network.
Your guide in harnessing the full potential of our platform.
Hear SOCRadar’s impressive achievements from our clients.
Automate and operationalize your security operations.
Consulting and professional services for cybersecurity excellence.
Industry, sector, and region-based in-depth research.
Discover the heartbeat of cyberspace through a collection showcasing the latest incidents.
Discover how XTI empowers organizations to proactively identify, mitigate, and respond to evolving cyber threats.
Register for our live webinars, and watch our on-demand webinars instantly.
Dive deep into the world of cyber threats, advanced analysis techniques, and cutting-edge strategies.
Stay informed and up-to-date on the latest cybersecurity trends.
Explore SOCRadar’s learning experience to fuel your cybersecurity journey with insights that exceed industry standards.
We offer expert-led, and exclusive trainings to help you master the latest in cybersecurity, trusted by over 2,000 top companies.
Scan the dark web to prevent your leaks from turning into real risks.
Instantly access dark web findings about your organization’s assets.
Check if there is anything about you in SOCRadar’s ever-expanding breach database.
Track threat actors and groups by country or industry for effective follow-up.
Explore threat actors’ tactics, techniques, activities, and detailed profiles targeting your industry or region.
All-in-one next-generation tools for investigating everyday events like phishing, malware, account breach, etc.
Power your search with SOCRadar’s IOC Radar.
Let’s get to know each other better.
Broaden your market reach and increase ARR with SOCRadar Extended Threat Intelligence.
Get informed of our upcoming events.
Latest news about our platform, company, and what’s being said about us.
Begin an extraordinary journey in your professional path with SOCRadar.
We’d like to hear from you.
SOCRadar Training Series – Mastering AI in Cybersecurity From Theory to Practice
Resources
The digital world is constantly under the threat of cyber attacks, and the emergence of new ransomware groups only intensifies this peril. One such group that has recently come into the spotlight is INC Ransom. This group has quickly gained notoriety for its sophisticated attacks and elusive nature. In this article, we will delve into the details of INC Ransom, exploring who they are, how they operate, and the implications of their activities. We will also provide insights into the security measures that can be implemented to protect against such threats.
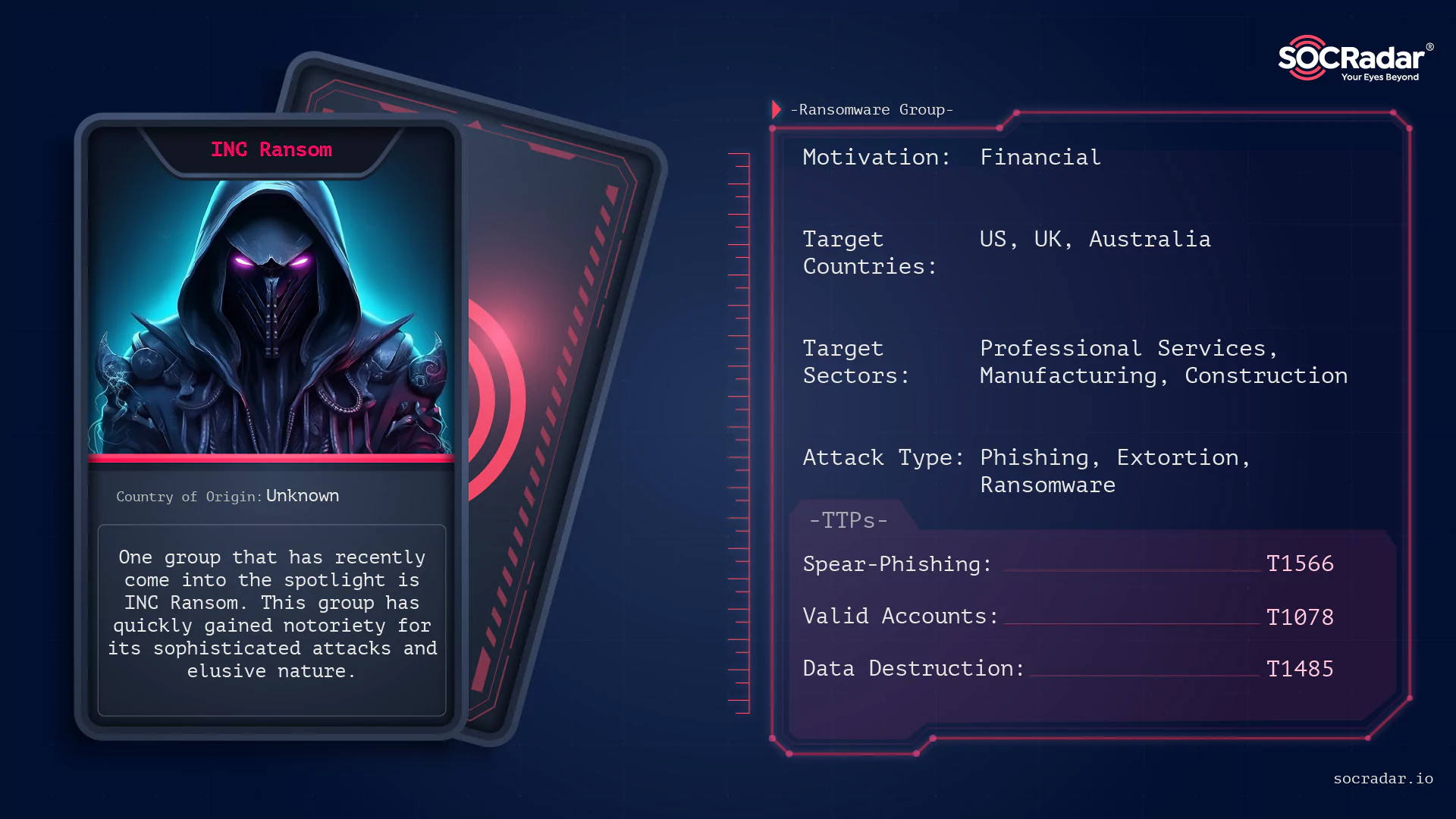
The threat actor card of INC Ransom
INC. Ransomware is a relatively new but highly sophisticated cybercriminal group that has rapidly gained notoriety in the realm of digital extortion. Emerging onto the cybercrime scene, this group has distinguished itself through its targeted ransomware attacks, primarily focusing on corporate and organizational networks.
Illustration of INC Ransom (generated using DALL-E 3)
Unlike many opportunistic ransomware operators, INC. Ransomware appears to carefully select its targets, often aiming at entities with substantial financial resources and sensitive data, which makes the potential payoff from their ransom demands significantly higher.
The group’s modus operandi involves a combination of advanced techniques, including spear-phishing campaigns to gain initial access, exploitation of known vulnerabilities (such as CVE-2023-3519 in Citrix NetScaler), and the use of both Commercial Off-The-Shelf (COTS) softwares and legitimate system tools (LOLBINs) for reconnaissance and lateral movement within a network. This approach not only demonstrates their technical prowess but also their ability to stay under the radar, making detection and prevention more challenging.
INC. Ransomware’s attacks are not just limited to encryption and locking of data; they also involve data theft and threats of public release, a tactic known as double extortion. This method adds an additional layer of pressure on the victims to comply with the ransom demands, as it puts at risk not just the accessibility of the data but also its confidentiality.
INC. Ransom employs a sophisticated and multi-staged approach to infiltrate and compromise target systems. Their attack methodology combines initial access through spear-phishing or exploiting vulnerabilities, such as CVE-2023-3519 in Citrix NetScaler, with a series of calculated steps to establish control and execute their ransomware. Here’s an overview of their attack process:
Initial Access and Reconnaissance: The group begins by gaining initial access, either through spear-phishing emails or by targeting vulnerable services. Once inside, they use a variety of tools for internal reconnaissance and lateral movement. These tools include NETSCAN.EXE for network scanning, MEGAsyncSetup64.EXE for file sharing and synchronization, ESENTUTL.EXE for database management, and AnyDesk.exe for remote desktop control.
Exploiting Remote Desktop Protocol (RDP): INC. Ransom frequently uses compromised credentials to access systems via RDP. During these sessions, they perform enumeration activities such as scanning for domain admins and testing network connections. This phase often involves brief connections to multiple servers, indicating a search for vulnerable points within the network.
Data Collection and Staging: Over the course of their attack, they abused legitimate software to collect and stage data for exfiltration. This involves using 7-Zip archival commands to gather data and employing native tools like Wordpad, Notepad, and MSPaint to inspect the contents of documents and images. They also install MEGASync on servers, presumably to facilitate the transfer of stolen data.
Lateral Movement and Credential Access: The attackers move laterally across the network, accessing multiple servers. They use tools like Advanced IP Scanner and Internet Explorer to explore the network and identify additional targets. During this phase, they also run credential access commands, indicative of using tools like lsassy.py, to extract login credentials from the systems.
File Encryption and Deployment: The final stage involves deploying the ransomware. They use a combination of wmic.exe and PSExec (disguised as winupd) to launch the file encryption executable across multiple endpoints. This phase is characterized by rapid command execution, indicating the use of batch files or scripts to automate the encryption process.
Troubleshooting and Adaptation: Interestingly, there are instances where the attackers encounter difficulties, such as the inability to run the encryption executable on certain servers. This is evidenced by multiple attempts to execute the ransomware with debug commands, showcasing their adaptability and persistence in overcoming challenges.
The first thing that caught our attention when we visited INC. Ransom’s TOR site was the dark and light modes:
INC Ransom TOR site in dark mode (Source: X)
Looking at the site in general, there is a section on the left side that leads to Leaks, a “Submit a Feedback” section, and a Twitter icon where “INC Ransom” is searched on Twitter when clicked. The rest of the page contains announcements made by INC. Ransom: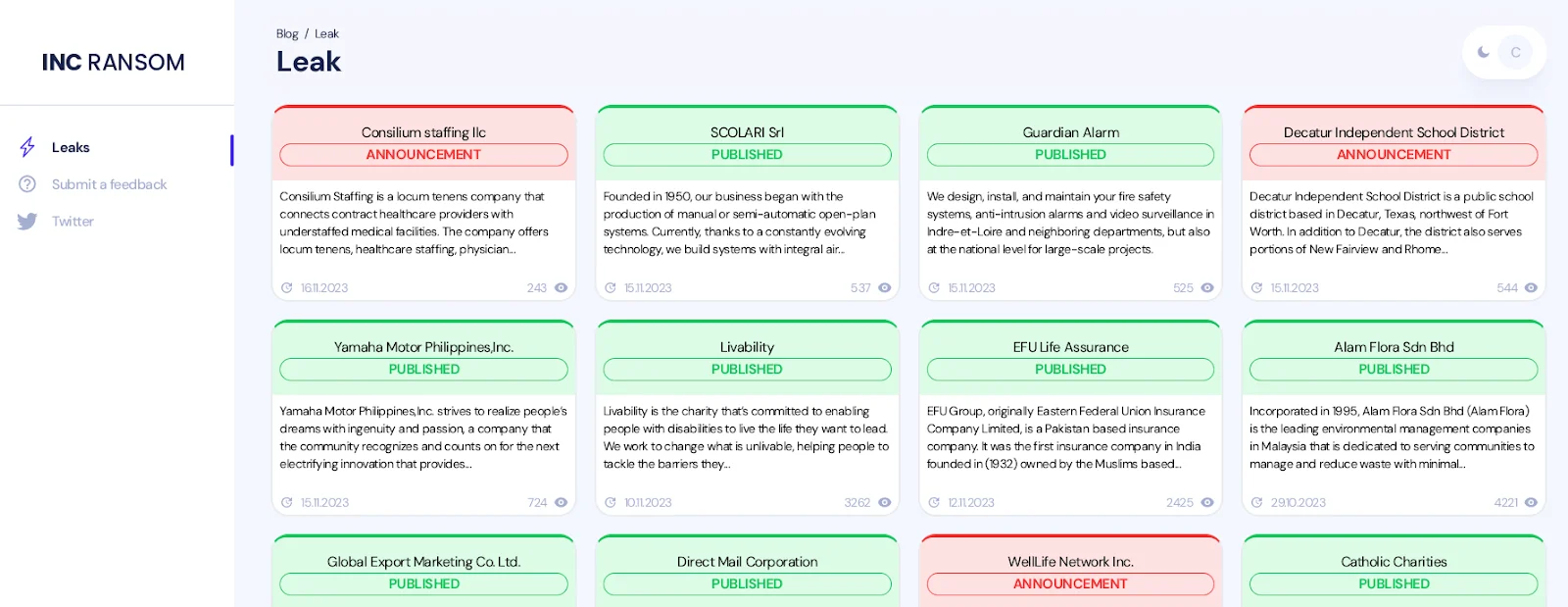
INC Ransom’s TOR site
Clicking on any leak announcement, a short description, the domain address of the victim organization, and proofs of the data leak, if any, can be found on the detail page.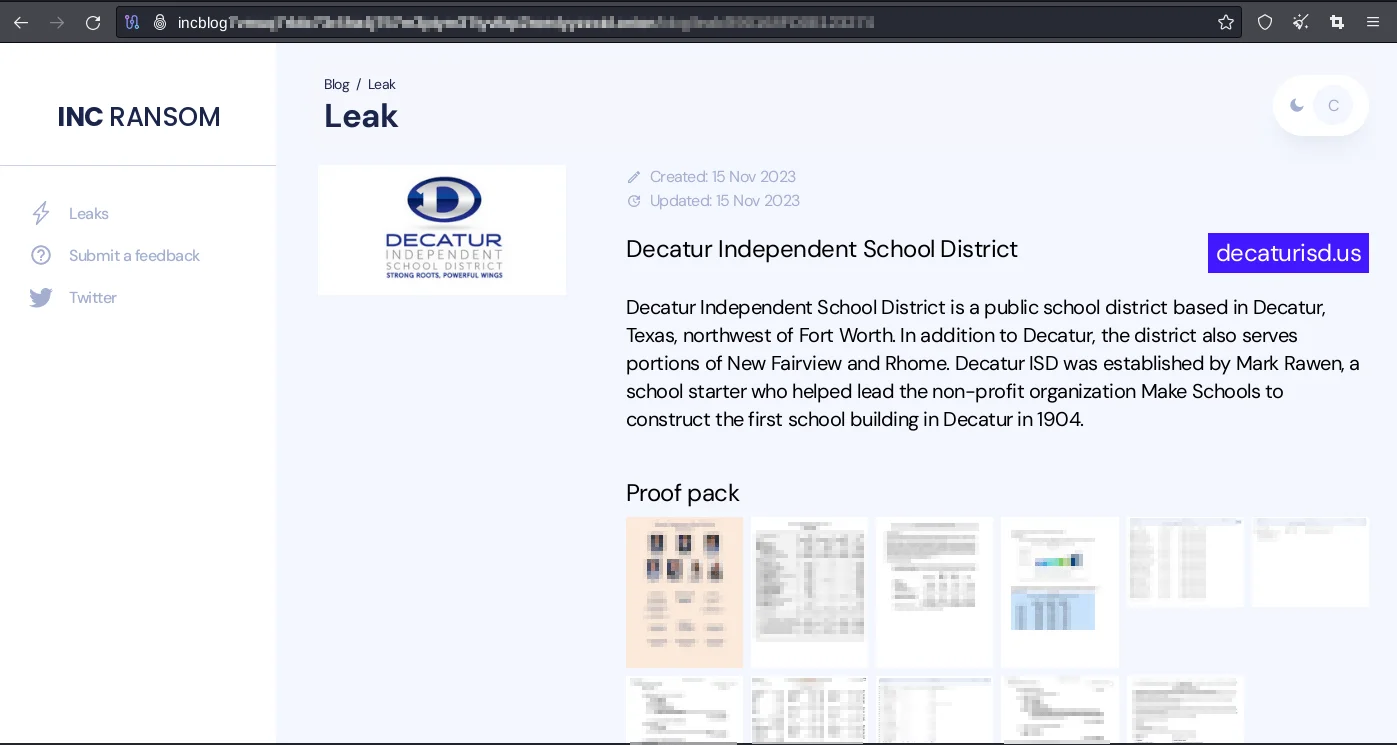
Decatur’s, one of the INC. Ransom’s victim, detailed Leak page
Additionally, the incapt[.]blog page that INC. Ransom has recently included on its page and where current leak announcements can be followed on the surface web: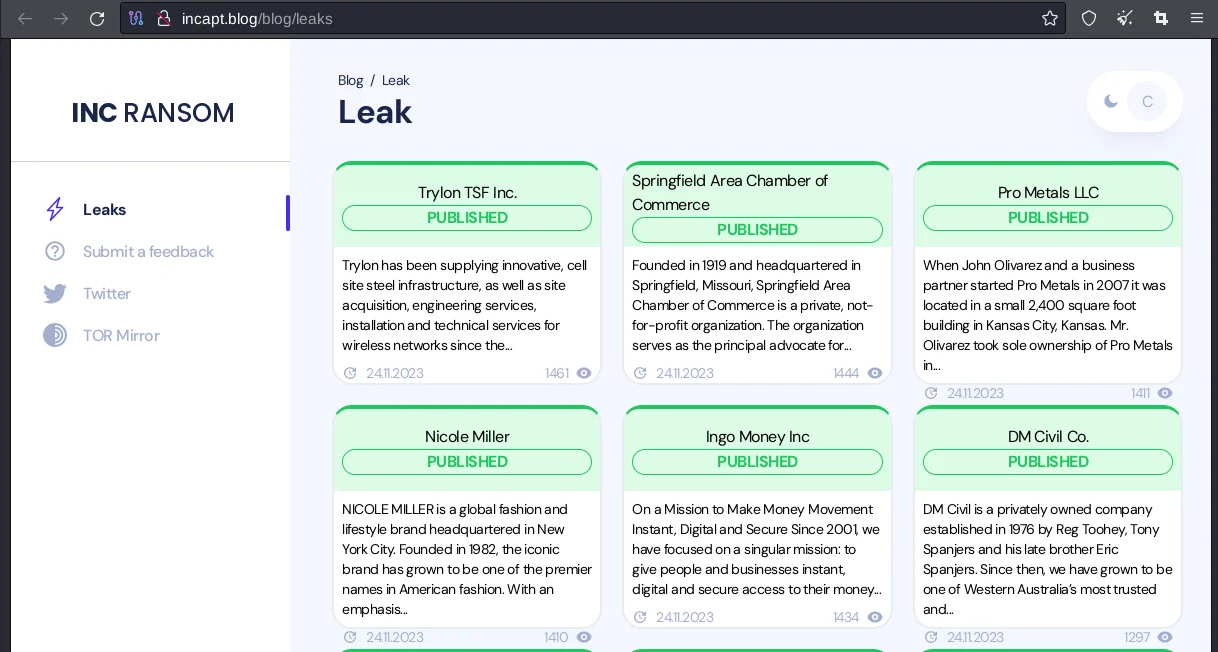
INC Ransom’s Leak Announcements
Looking at the industries in which INC. Ransom’s victim organizations work, the majority are in Professional Services, Manufacturing and Construction: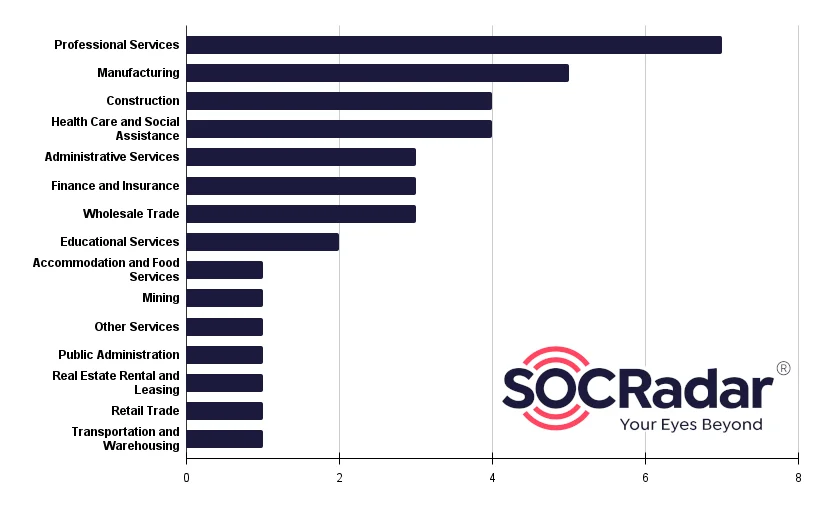
INC. Ransom’s Targeted Sectors
The majority of the organizations targeted by “INC. Ransom” are based in North America and Europe:
INC. Ransom Targeted Countries
In terms of distribution, it is observed that “INC. Ransom” mostly targets organizations operating in the United States(57.9%):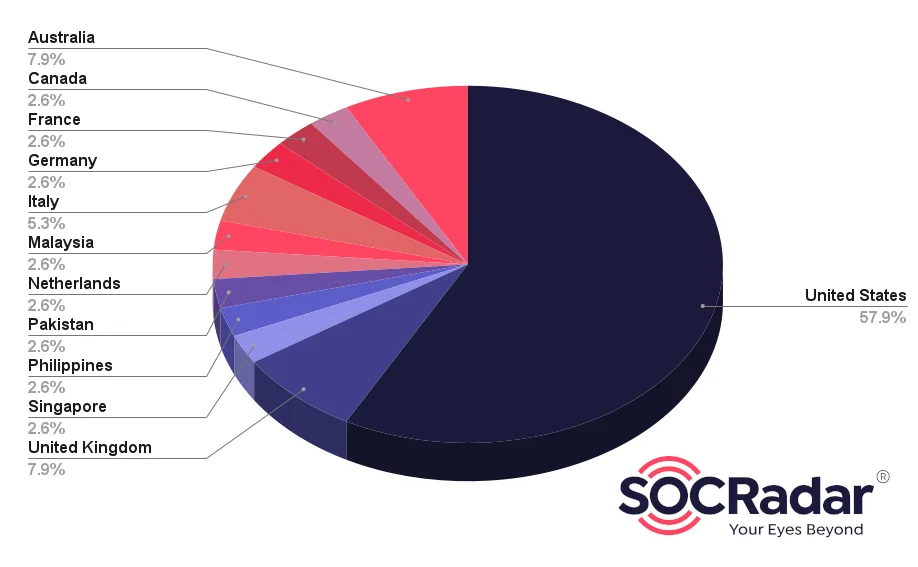
Targets Distribution
Trylon:
Trylon
Springfield:
Springfield
The emergence and activities of the INC. Ransom group represent a significant threat in the cybersecurity landscape. Their sophisticated and multi-layered attack methodology, which includes exploiting vulnerabilities, using a mix of commercial and legitimate tools for reconnaissance and lateral movement, and executing a carefully planned ransomware deployment, highlights the evolving nature of cyber threats.
INC. Ransom’s ability to adapt and troubleshoot during their attacks, as well as their strategic use of tools for data collection, staging, and encryption, demonstrate a high level of technical expertise and planning.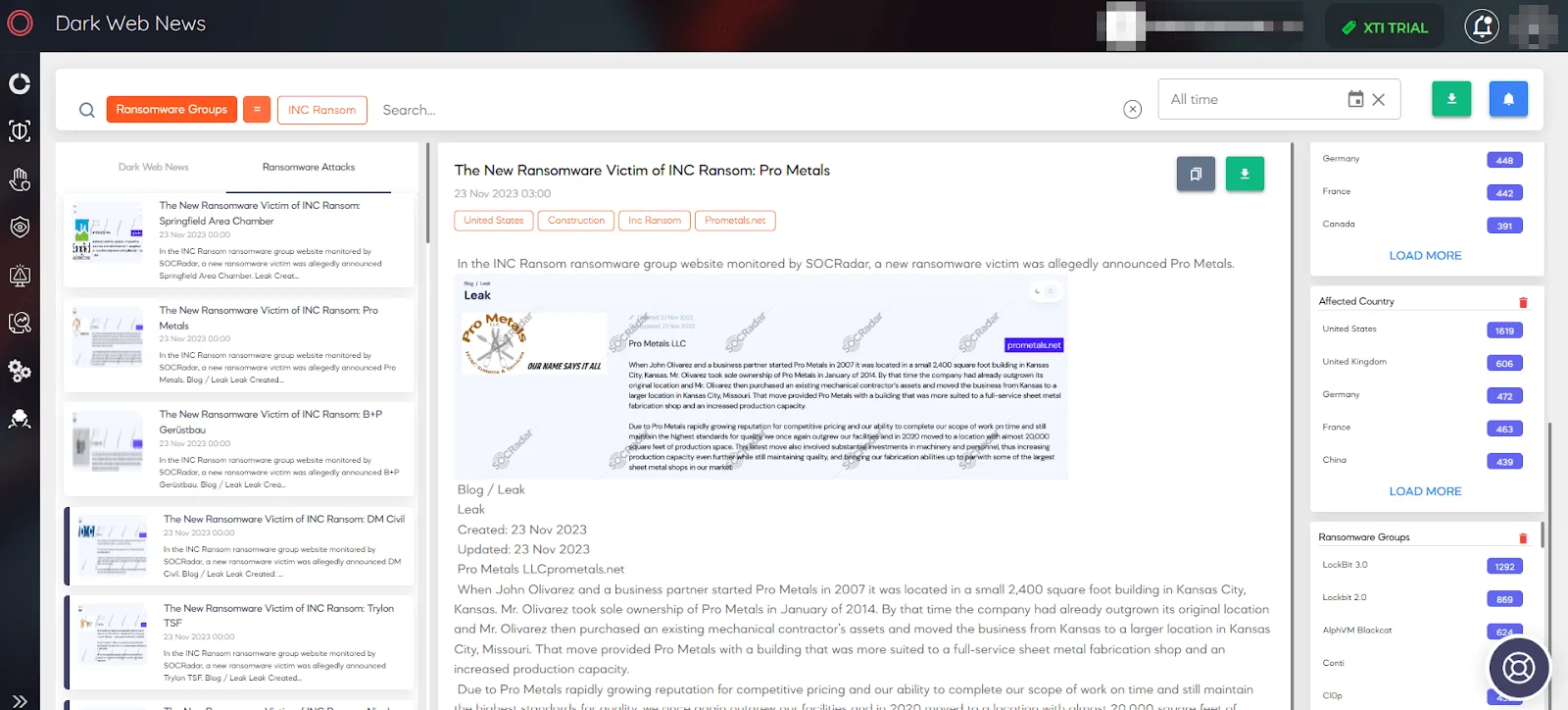
SOCRadar Dark Web News
To defend against the sophisticated tactics of INC. Ransom, organizations need to adopt a multi-layered security approach. Here are some key recommendations to enhance cybersecurity defenses against such ransomware threats:
Regularly Update and Patch Systems: Ensure that all software, especially critical and widely-used applications like Citrix NetScaler, are regularly updated and patched. This helps to close vulnerabilities that could be exploited by ransomware groups.
Enhanced Email Security: Since spear-phishing is a common initial access vector, implement advanced email security solutions. These should include phishing detection, sandboxing for email attachments, and user training to recognize and report suspicious emails.
Robust Endpoint Protection: Deploy advanced Endpoint Protection Platforms (EPP) that can detect, prevent, and respond to threats using techniques like behavioral analysis and machine learning.
Network Segmentation and Monitoring: Segment your network to limit lateral movement by attackers. Use Intrusion Detection Systems (IDS) and Intrusion Prevention Systems (IPS) to monitor network traffic for suspicious activities.
Implement Multi-Factor Authentication (MFA): MFA adds an extra layer of security for accessing sensitive systems and data, making it harder for attackers to gain access even if they have compromised credentials.
Regular Backups and Data Encryption: Regularly back up critical data and ensure it’s stored securely, preferably off site or in the cloud. Encrypt sensitive data to add an additional layer of protection.
Incident Response Planning: Have a well-defined incident response plan that includes procedures for isolating affected systems, eradicating the ransomware, and restoring data from backups.
Employee Awareness and Training: Regularly train employees on cybersecurity best practices, including how to recognize phishing attempts and the importance of using strong, unique passwords.
Use of Advanced Threat Intelligence: Stay informed about the latest ransomware tactics and Indicators of Compromise (IoCs) through threat intelligence feeds and cybersecurity reports.
Regular Security Audits and Vulnerability Assessments: Conduct regular security audits and vulnerability assessments to identify and mitigate potential security gaps in your network and systems.
Subscribe to our newsletter and stay updated on the latest insights!
PROTECTION OF PERSONAL DATA COOKIE POLICY FOR THE INTERNET SITE
Protecting your personal data is one of the core principles of our organization, SOCRadar, which operates the internet site (www.socradar.com). This Cookie Usage Policy (“Policy”) explains the types of cookies used and the conditions under which they are used to all website visitors and users.
Cookies are small text files stored on your computer or mobile device by the websites you visit.
Cookies are commonly used to provide you with a personalized experience while using a website, enhance the services offered, and improve your overall browsing experience, contributing to ease of use while navigating a website. If you prefer not to use cookies, you can delete or block them through your browser settings. However, please be aware that this may affect your usage of our website. Unless you change your cookie settings in your browser, we will assume that you accept the use of cookies on this site.
1. WHAT KIND OF DATA IS PROCESSED IN COOKIES?
Cookies on websites collect data related to your browsing and usage preferences on the device you use to visit the site, depending on their type. This data includes information about the pages you access, the services and products you explore, your preferred language choice, and other preferences.
2. WHAT ARE COOKIES AND WHAT ARE THEIR PURPOSES?
Cookies are small text files stored on your device or web server by the websites you visit through your browsers. These small text files, containing your preferred language and other settings, help us remember your preferences on your next visit and assist us in making improvements to our services to enhance your experience on the site. This way, you can have a better and more personalized user experience on your next visit.
The main purposes of using cookies on our Internet Site are as follows:
3. TYPES OF COOKIES USED ON OUR INTERNET SITE 3.1. Session Cookies
Session cookies ensure the smooth operation of the internet site during your visit. They are used for purposes such as ensuring the security and continuity of our sites and your visits. Session cookies are temporary cookies and are deleted when you close your browser; they are not permanent.
3.2. Persistent Cookies
These cookies are used to remember your preferences and are stored on your device through browsers. Persistent cookies remain stored on your device even after you close your browser or restart your computer. These cookies are stored in your browser’s subfolders until deleted from your browser’s settings. Some types of persistent cookies can be used to provide personalized recommendations based on your usage purposes.
With persistent cookies, when you revisit our website with the same device, the website checks if a cookie created by our website exists on your device. If so, it is understood that you have visited the site before, and the content to be presented to you is determined accordingly, offering you a better service.
3.3. Mandatory/Technical Cookies
Mandatory cookies are essential for the proper functioning of the visited internet site. The purpose of these cookies is to provide necessary services by ensuring the operation of the site. For example, they allow access to secure sections of the internet site, use of its features, and navigation.
3.4. Analytical Cookies
These cookies gather information about how the website is used, the frequency and number of visits, and show how visitors navigate to the site. The purpose of using these cookies is to improve the operation of the site, increase its performance, and determine general trend directions. They do not contain data that can identify visitors. For example, they show the number of error messages displayed or the most visited pages.
3.5. Functional Cookies
Functional cookies remember the choices made by visitors within the site and recall them during the next visit. The purpose of these cookies is to provide ease of use to visitors. For example, they prevent the need to re-enter the user’s password on each page visited by the site user.
3.6. Targeting/Advertising Cookies
They measure the effectiveness of advertisements shown to visitors and calculate how many times ads are displayed. The purpose of these cookies is to present personalized advertisements to visitors based on their interests.
Similarly, they determine the specific interests of visitors’ navigation and present appropriate content. For example, they prevent the same advertisement from being shown again to the visitor in a short period.
4. HOW TO MANAGE COOKIE PREFERENCES?
To change your preferences regarding the use of cookies, block or delete cookies, you only need to change your browser settings.
Many browsers offer options to accept or reject cookies, only accept certain types of cookies, or receive notifications from the browser when a website requests to store cookies on your device.
Also, it is possible to delete previously saved cookies from your browser.
If you disable or reject cookies, you may need to manually adjust some preferences, and certain features and services on the website may not work properly as we will not be able to recognize and associate with your account. You can change your browser settings by clicking on the relevant link from the table below.
5. EFFECTIVE DATE OF THE INTERNET SITE PRIVACY POLICY
The Internet Site Privacy Policy is dated The effective date of the Policy will be updated if the entire Policy or specific sections are renewed. The Privacy Policy is published on the Organization’s website (www.socradar.com) and made accessible to relevant individuals upon request.
SOCRadar
Address: 651 N Broad St, Suite 205 Middletown, DE 19709 USA
Phone: +1 (571) 249-4598
Email: [email protected]
Website: www.socradar.com
