
Threat intelligence enriched with External Attack Surface Management, Brand Protection, and Dark Web Radar.
Protect your business from the dangers lurking in the hidden corners of the internet.
Effective threat hunting and threat actor tracking with behavioral analytics.
Discover your assets with a hacker mindset.
Stay ahead of threat actors with actionable intelligence alerts.
Evaluate the security posture of your entire supply network.
Your guide in harnessing the full potential of our platform.
Hear SOCRadar’s impressive achievements from our clients.
Automate and operationalize your security operations.
Consulting and professional services for cybersecurity excellence.
Industry, sector, and region-based in-depth research.
Discover the heartbeat of cyberspace through a collection showcasing the latest incidents.
Discover how XTI empowers organizations to proactively identify, mitigate, and respond to evolving cyber threats.
Register for our live webinars, and watch our on-demand webinars instantly.
Dive deep into the world of cyber threats, advanced analysis techniques, and cutting-edge strategies.
Stay informed and up-to-date on the latest cybersecurity trends.
Explore SOCRadar’s learning experience to fuel your cybersecurity journey with insights that exceed industry standards.
We offer expert-led, and exclusive trainings to help you master the latest in cybersecurity, trusted by over 2,000 top companies.
Scan the dark web to prevent your leaks from turning into real risks.
Instantly access dark web findings about your organization’s assets.
Check if there is anything about you in SOCRadar’s ever-expanding breach database.
Track threat actors and groups by country or industry for effective follow-up.
Explore threat actors’ tactics, techniques, activities, and detailed profiles targeting your industry or region.
All-in-one next-generation tools for investigating everyday events like phishing, malware, account breach, etc.
Power your search with SOCRadar’s IOC Radar.
Let’s get to know each other better.
Broaden your market reach and increase ARR with SOCRadar Extended Threat Intelligence.
Get informed of our upcoming events.
Latest news about our platform, company, and what’s being said about us.
Begin an extraordinary journey in your professional path with SOCRadar.
We’d like to hear from you.
SOCRadar Training Series – Mastering AI in Cybersecurity From Theory to Practice
Resources
In 2023, Abyss Locker ransomware emerged as a critical cybersecurity threat, aggressively targeting Windows and Linux systems across industries like finance, manufacturing, and technology. Known for its advanced encryption and multi-extortion tactics, Abyss Locker disrupts operations and demands hefty ransoms, making it a top concern for businesses worldwide.
Abyss Ransomware (also known as Abyss Locker) is a ransomware group that first appeared on the cybersecurity radar in 2023. Emerging as a potent threat, this group quickly gained notoriety for its aggressive targeting of various industries, including finance, manufacturing, healthcare, and information technology. Abyss Ransomware is believed to have roots in the infamous HelloKitty ransomware, leveraging its source code to develop its malicious operations.
Initially, the group focused on Windows systems, but it soon expanded its capabilities to include Linux environments, particularly VMware ESXi virtualized platforms. This expansion was marked by the introduction a specialized Linux encryptor designed to infiltrate and disrupt critical virtual environments. The group’s ability to adapt and evolve tactics has made it a significant player in ransomware.
Abyss Ransomware dark web platform
Abyss Ransomware operates as a multi-extortion ransomware group. It encrypts victims’ files and exfiltrates sensitive data, used as leverage in ransom negotiations. Victims who do not comply with the ransom demands face the threat of their data being exposed on a TOR-based website operated by the group.
The group’s operations are characterized by sophisticated tactics, including lateral movement within networks, termination of critical services and processes, and advanced encryption techniques. Abyss Ransomware has shown a particular focus on the United States, targeting sectors that include medical institutions, manufacturing companies, and tech firms. Their attacks have caused significant disruptions, often forcing organizations to negotiate and pay hefty ransoms to avoid further damage.
Despite its relatively recent emergence, the group has established itself as a formidable ransomware threat, demonstrating both technical prowess and a ruthless approach to extortion.
According to the researchers, Abyss Ransomware employs various sophisticated Tactics, Techniques, and Procedures (TTPs) to maximize its impact on targeted systems. The group’s operations are notable for their technical complexity and strategic execution, particularly in Windows and Linux environments.
Notably, Abyss has seen two main versions (v1 and v2), with v2 introducing updates primarily in ransom note messaging and TOR addresses while maintaining the core functionality of v1. Here’s a breakdown of how Abyss Ransomware operates:
Abyss Ransomware typically gains initial access to its targets through phishing emails, exploiting weak SSH configurations, or leveraging known vulnerabilities in exposed servers. The group has been observed using brute-force attacks against SSH to establish a foothold, particularly in Linux environments. Once inside, Abyss rapidly deploys its payload to begin the encryption process.
According to the researchers, the Windows variant of Abyss Ransomware is highly destructive and strategically turns off critical services and processes before beginning encryption. Here’s a closer look at the process: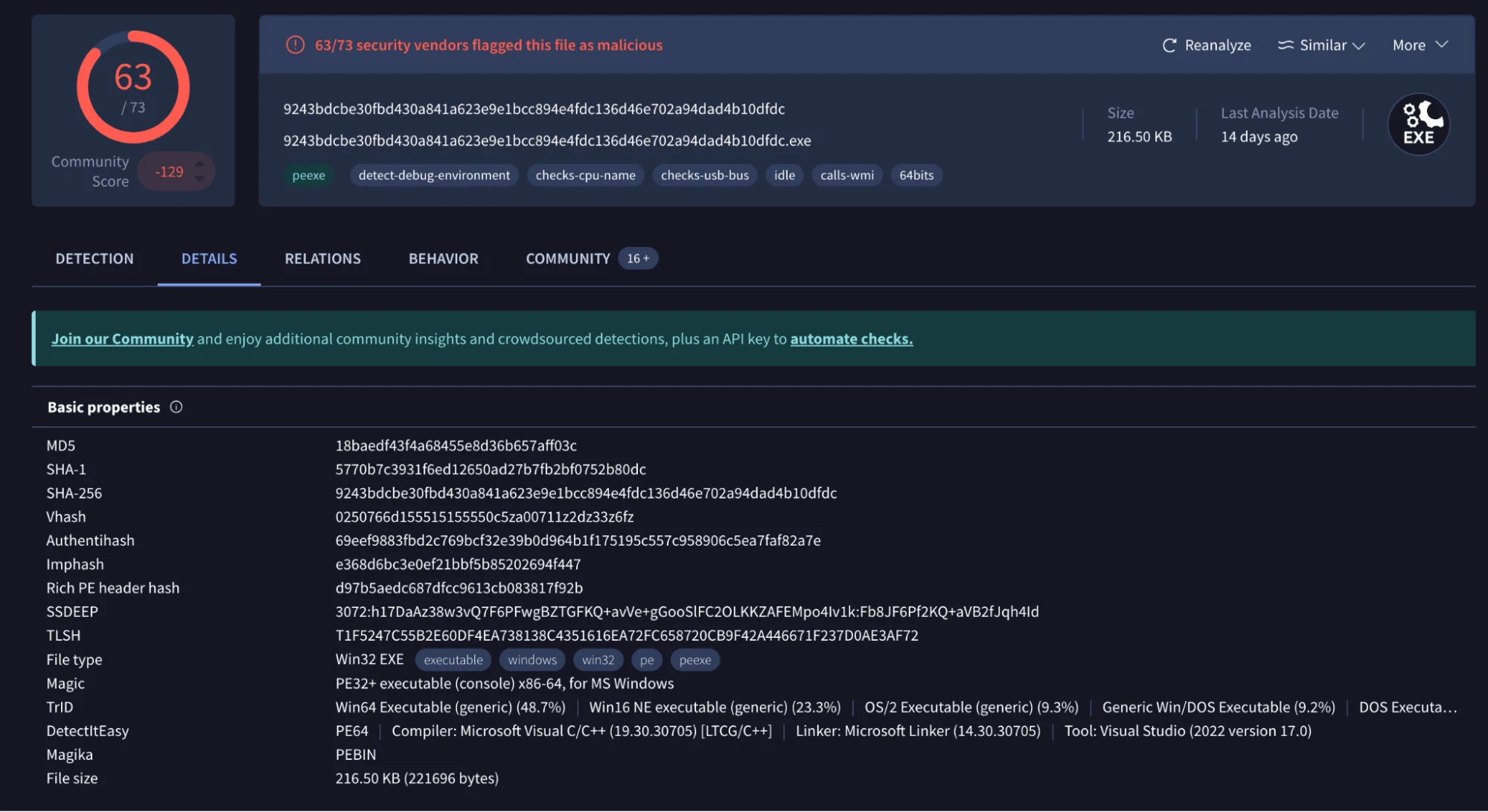
Basic properties of a known sample, written in C++ (VirusTotal)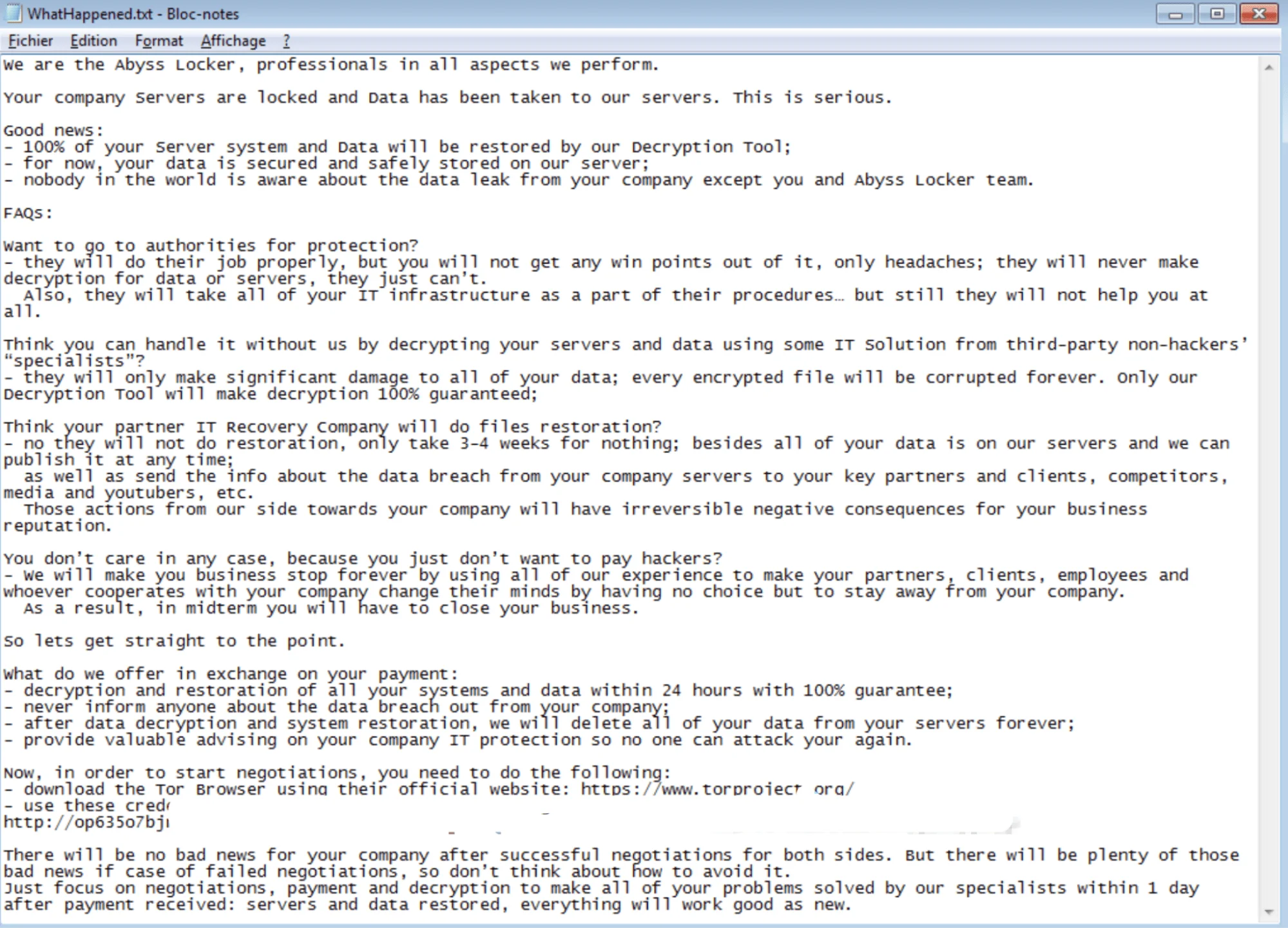
WhatHappened.txt (X)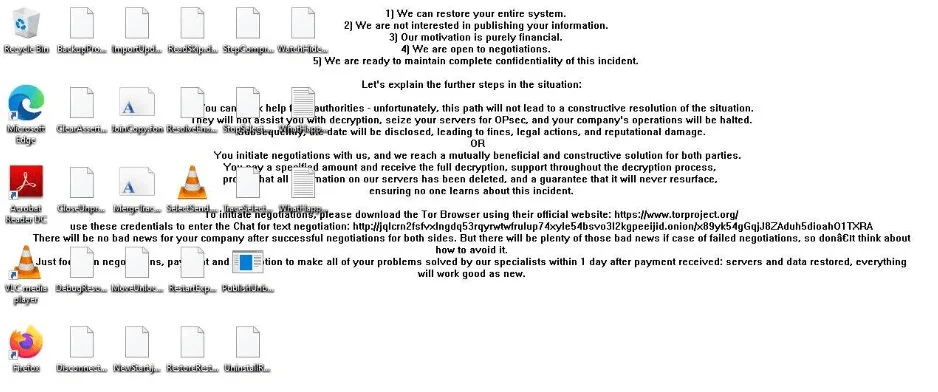
Abyss Ransomware replaces the victim’s desktop wallpaper with a ransom note (X)
The Linux variant of Abyss Ransomware is particularly dangerous for environments utilizing VMware ESXi virtualized infrastructure. Here’s how it operates: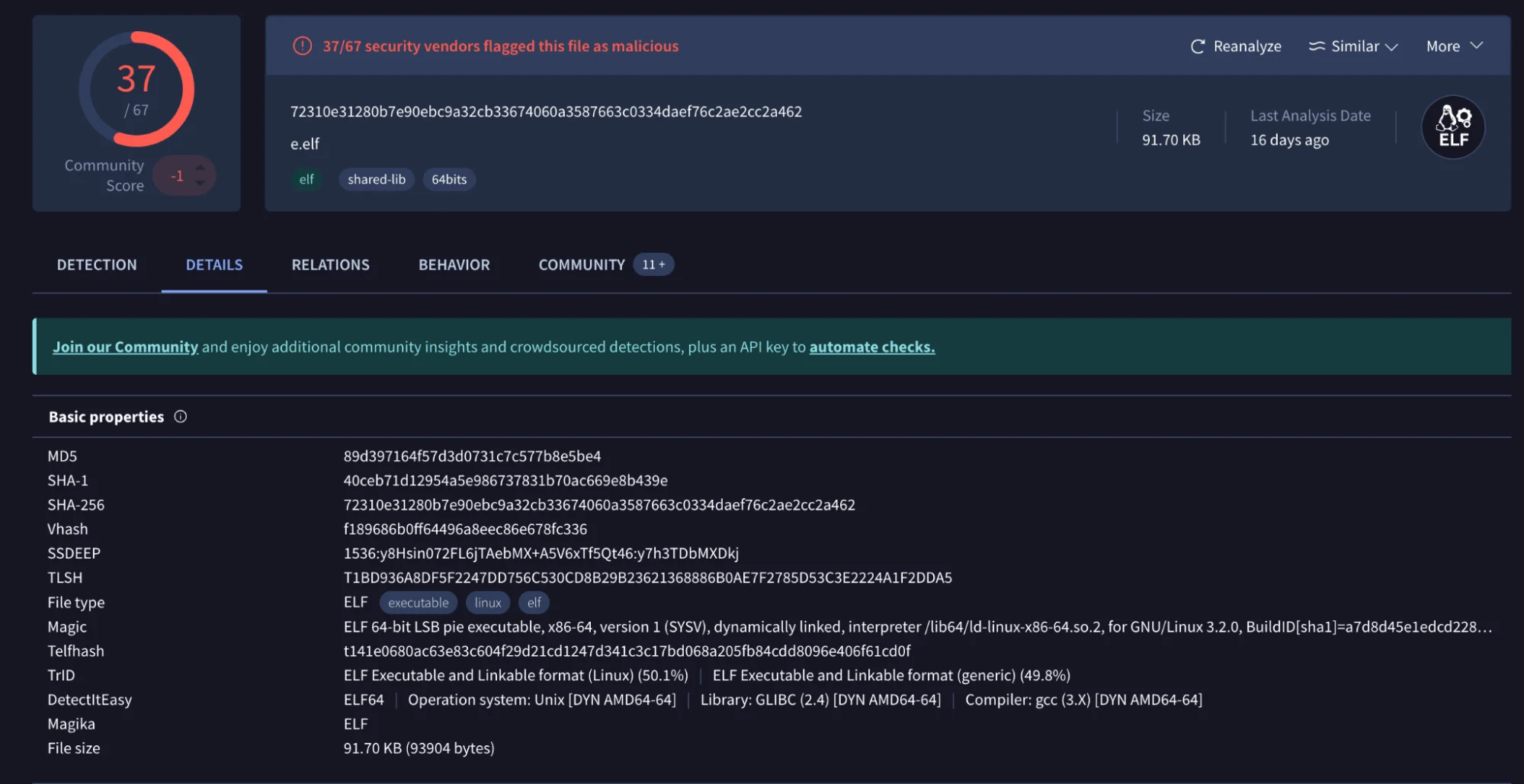
Basic properties of a known sample (VirusTotal)
In addition to encryption, Abyss Ransomware engages in data exfiltration, stealing sensitive information before locking down the victim’s files. This data is used as additional leverage in ransom negotiations. If the victim fails to pay, the group threatens to release the data publicly on their TOR-based leak site, which could lead to significant reputational damage and legal consequences for the victim.
Abyss Ransomware’s operations demonstrate a high level of sophistication, with carefully designed strategies to ensure maximum disruption and leverage against its victims. Its ability to operate across multiple platforms and utilize advanced encryption and exfiltration techniques makes it a significant threat in the current cybersecurity landscape.
Abyss ransomware has been highly active, targeting various industries and countries. Since its emergence, the group has launched numerous attacks, with a significant concentration in the United States.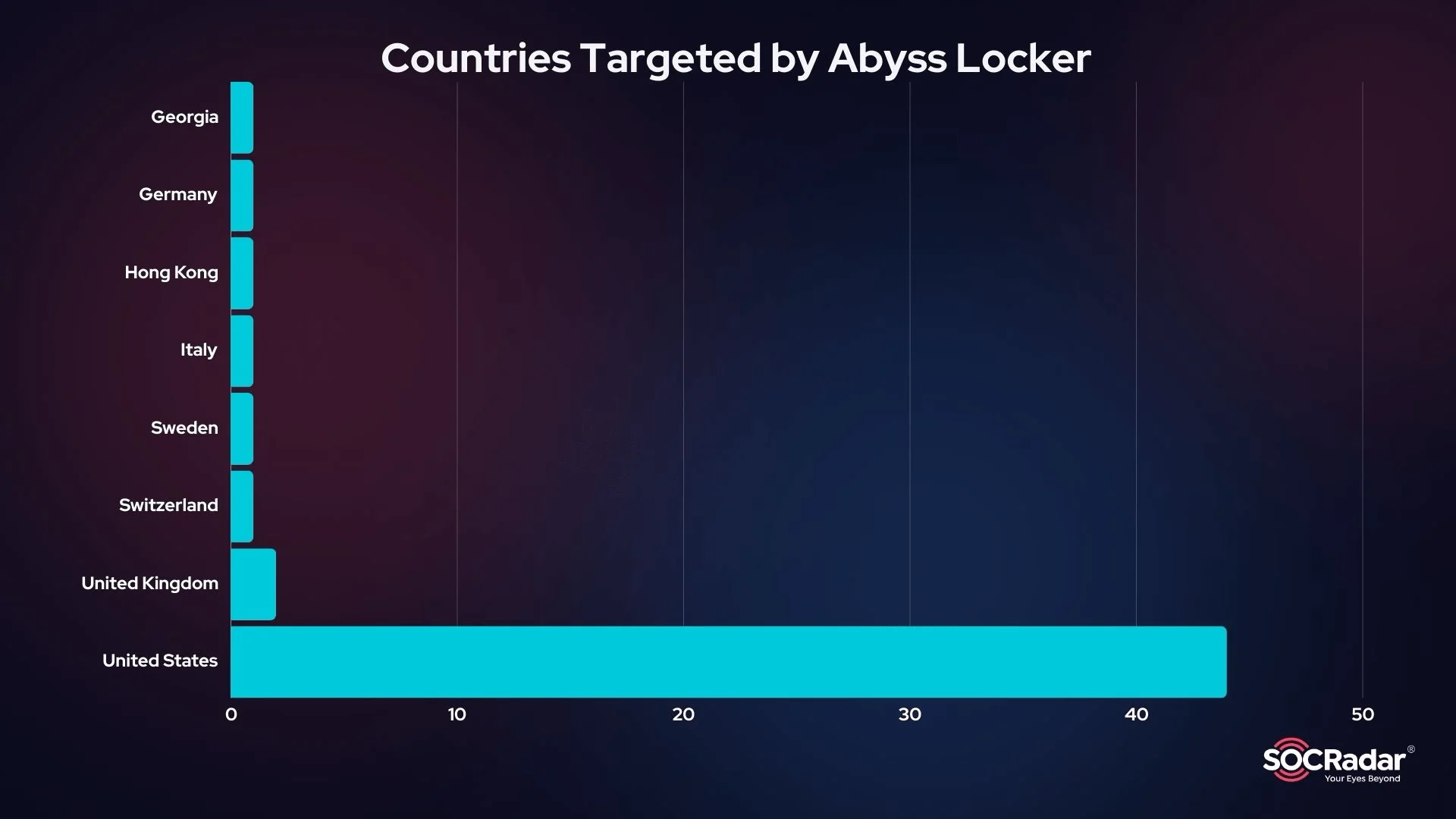
Targeted Countries So Far
The Abyss ransomware group has primarily focused on the United States, with 48 out of the total attacks occurring there. Other countries affected include Germany, the United Kingdom, Sweden, Switzerland, Canada, Georgia, Italy, and Hong Kong.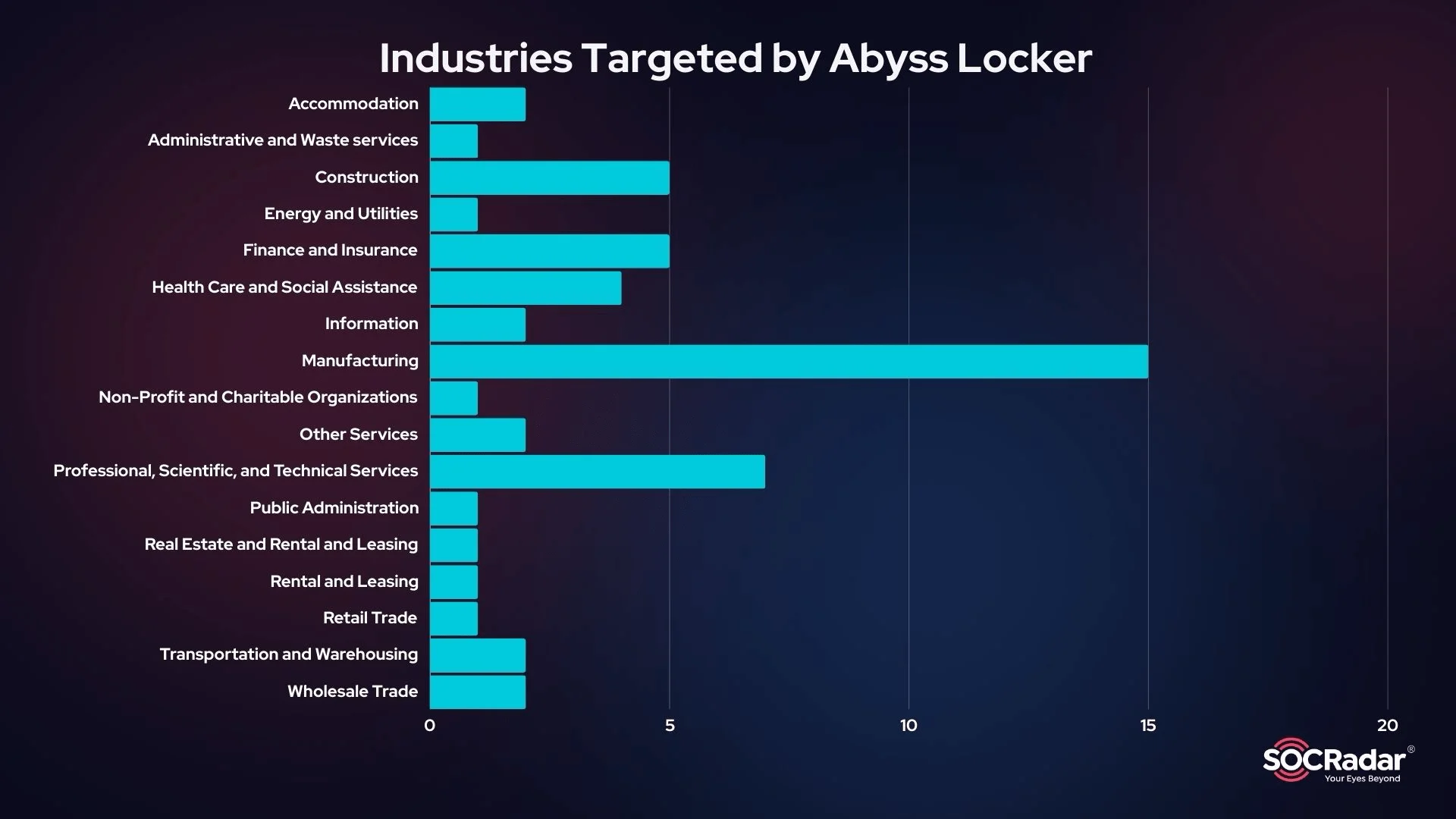
Targeted Industries So Far
Abyss has shown a particular interest in the Manufacturing sector, which has been hit the hardest. Other targeted industries include Finance and Insurance, Professional, Scientific, and Technical Services, Health Care and Social Assistance, and Construction.
Defending against Abyss Locker ransomware requires a multifaceted approach that incorporates advanced security tools and proactive strategies. Here are the key steps organizations should take:
By following these mitigation and protection strategies, organizations can significantly reduce their vulnerability to Abyss Locker ransomware and similar threats. A proactive, layered approach to security will help maintain resilience against the constantly evolving landscape of cyber threats.
SOCRadar provides comprehensive support to organizations facing the threat of ransomware like Abyss Locker, through a variety of advanced cybersecurity tools and services.
One of the key offerings is the Extended Threat Intelligence (XTI) platform, which delivers real-time threat detection capabilities. This platform monitors the evolving threat landscape continuously, enabling organizations to identify potential ransomware threats before they cause significant harm. By providing actionable insights into emerging threats, including specific Indicators of Compromise (IoCs) and Tactics, Techniques, and Procedures (TTPs) used by Abyss Ransomware, SOCRadar helps organizations stay one step ahead of attackers.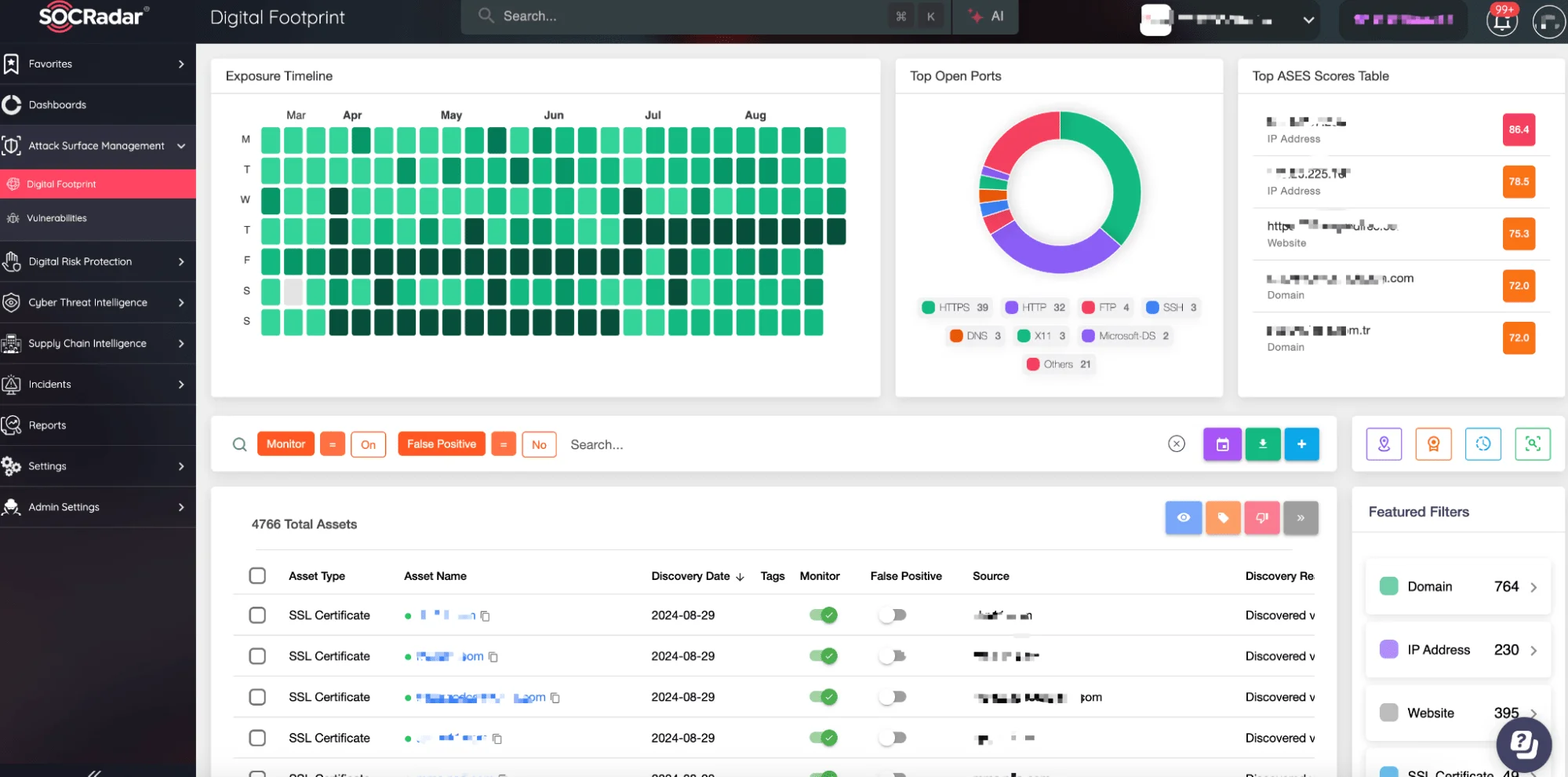
SOCRadar Attack Surface Management, Digital Footprint
Another crucial service is Attack Surface Management, which helps reduce vulnerabilities across your digital footprint. SOCRadar continuously scans for potential security gaps, providing organizations with a clear understanding of their exposure to external threats. By identifying and managing these vulnerabilities proactively, SOCRadar enables organizations to effectively minimize the risk of exploitation by ransomware like Abyss Locker.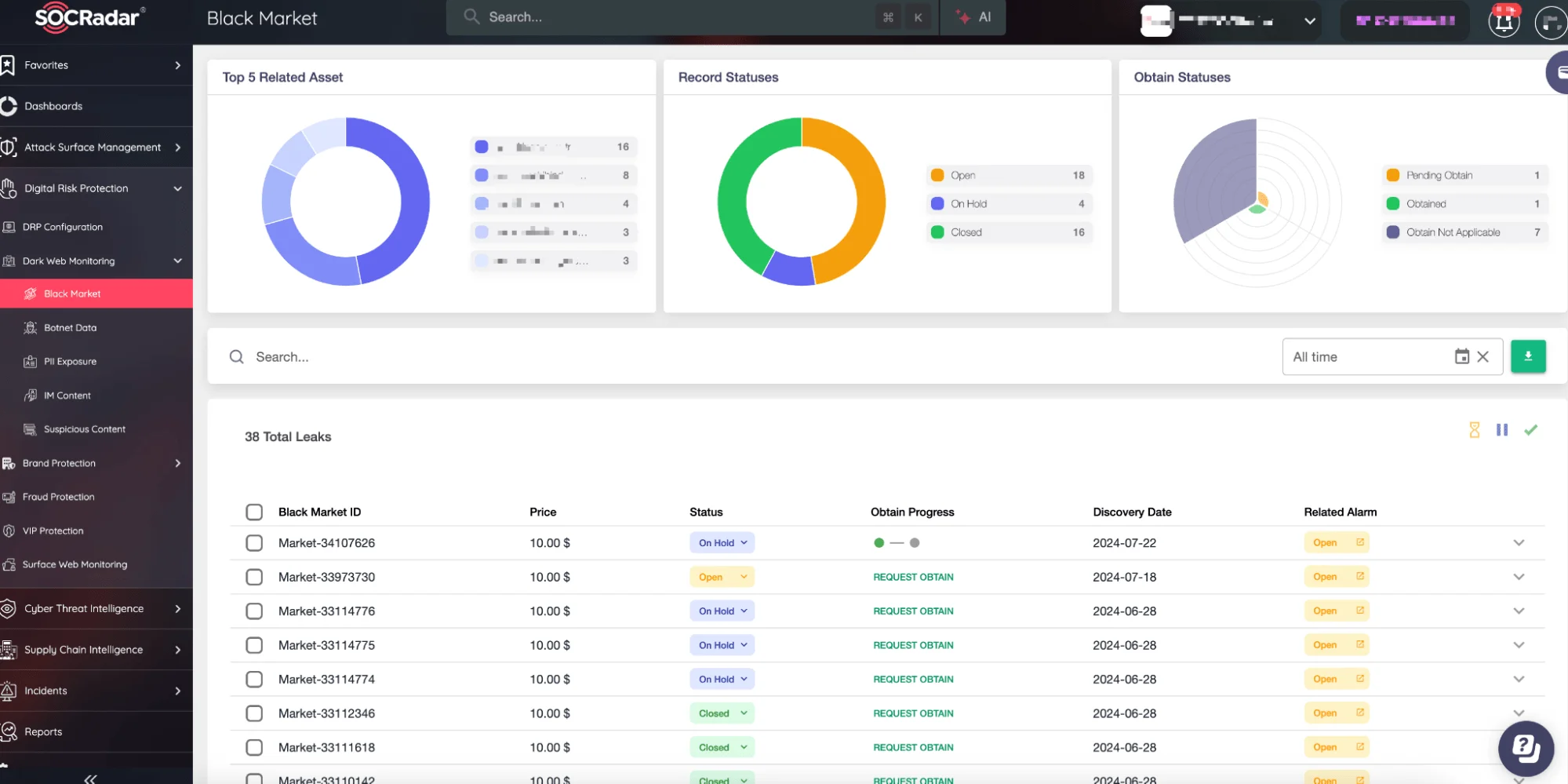
SOCRadar Dark Web Monitoring
In addition to threat detection, SOCRadar’s Dark Web Monitoring service plays a crucial role in identifying potential risks early. Abyss Ransomware, like many other ransomware groups, may expose stolen data on dark web forums as part of their extortion strategy. SOCRadar’s monitoring service scans these hidden parts of the internet, detecting any mentions of your organization, leaked data, or indicators of an impending attack. By identifying these threats early, SOCRadar enables you to take preventive actions to protect your data and minimize potential damage.
Abyss Ransomware group has rapidly emerged as a formidable ransomware threat, targeting various industries with sophisticated tactics and advanced encryption techniques. Its ability to compromise both Windows and Linux environments, particularly within VMware ESXi virtualized platforms, underscores the need for organizations to adopt a robust and multifaceted cybersecurity strategy.
Proactive measures, such as regular system updates, strong authentication practices, comprehensive backup and disaster recovery planning, and continuous monitoring, are essential to mitigating the risks posed by Abyss Ransomware. Leveraging advanced tools like SOCRadar’s Extended Threat Intelligence, Attack Surface Management, and Dark Web Monitoring services further enhances an organization’s ability to detect, prevent, and respond to these threats effectively.
Abyss Locker ransomware employs a variety of tactics, techniques, and procedures (TTPs) that align with the MITRE ATT&CK framework. Understanding these TTPs is crucial for developing effective defense strategies against this threat. Below are the key TTPs associated with Abyss Locker:
Hash Values:
File Indicators:
Subscribe to our newsletter and stay updated on the latest insights!
PROTECTION OF PERSONAL DATA COOKIE POLICY FOR THE INTERNET SITE
Protecting your personal data is one of the core principles of our organization, SOCRadar, which operates the internet site (www.socradar.com). This Cookie Usage Policy (“Policy”) explains the types of cookies used and the conditions under which they are used to all website visitors and users.
Cookies are small text files stored on your computer or mobile device by the websites you visit.
Cookies are commonly used to provide you with a personalized experience while using a website, enhance the services offered, and improve your overall browsing experience, contributing to ease of use while navigating a website. If you prefer not to use cookies, you can delete or block them through your browser settings. However, please be aware that this may affect your usage of our website. Unless you change your cookie settings in your browser, we will assume that you accept the use of cookies on this site.
1. WHAT KIND OF DATA IS PROCESSED IN COOKIES?
Cookies on websites collect data related to your browsing and usage preferences on the device you use to visit the site, depending on their type. This data includes information about the pages you access, the services and products you explore, your preferred language choice, and other preferences.
2. WHAT ARE COOKIES AND WHAT ARE THEIR PURPOSES?
Cookies are small text files stored on your device or web server by the websites you visit through your browsers. These small text files, containing your preferred language and other settings, help us remember your preferences on your next visit and assist us in making improvements to our services to enhance your experience on the site. This way, you can have a better and more personalized user experience on your next visit.
The main purposes of using cookies on our Internet Site are as follows:
3. TYPES OF COOKIES USED ON OUR INTERNET SITE 3.1. Session Cookies
Session cookies ensure the smooth operation of the internet site during your visit. They are used for purposes such as ensuring the security and continuity of our sites and your visits. Session cookies are temporary cookies and are deleted when you close your browser; they are not permanent.
3.2. Persistent Cookies
These cookies are used to remember your preferences and are stored on your device through browsers. Persistent cookies remain stored on your device even after you close your browser or restart your computer. These cookies are stored in your browser’s subfolders until deleted from your browser’s settings. Some types of persistent cookies can be used to provide personalized recommendations based on your usage purposes.
With persistent cookies, when you revisit our website with the same device, the website checks if a cookie created by our website exists on your device. If so, it is understood that you have visited the site before, and the content to be presented to you is determined accordingly, offering you a better service.
3.3. Mandatory/Technical Cookies
Mandatory cookies are essential for the proper functioning of the visited internet site. The purpose of these cookies is to provide necessary services by ensuring the operation of the site. For example, they allow access to secure sections of the internet site, use of its features, and navigation.
3.4. Analytical Cookies
These cookies gather information about how the website is used, the frequency and number of visits, and show how visitors navigate to the site. The purpose of using these cookies is to improve the operation of the site, increase its performance, and determine general trend directions. They do not contain data that can identify visitors. For example, they show the number of error messages displayed or the most visited pages.
3.5. Functional Cookies
Functional cookies remember the choices made by visitors within the site and recall them during the next visit. The purpose of these cookies is to provide ease of use to visitors. For example, they prevent the need to re-enter the user’s password on each page visited by the site user.
3.6. Targeting/Advertising Cookies
They measure the effectiveness of advertisements shown to visitors and calculate how many times ads are displayed. The purpose of these cookies is to present personalized advertisements to visitors based on their interests.
Similarly, they determine the specific interests of visitors’ navigation and present appropriate content. For example, they prevent the same advertisement from being shown again to the visitor in a short period.
4. HOW TO MANAGE COOKIE PREFERENCES?
To change your preferences regarding the use of cookies, block or delete cookies, you only need to change your browser settings.
Many browsers offer options to accept or reject cookies, only accept certain types of cookies, or receive notifications from the browser when a website requests to store cookies on your device.
Also, it is possible to delete previously saved cookies from your browser.
If you disable or reject cookies, you may need to manually adjust some preferences, and certain features and services on the website may not work properly as we will not be able to recognize and associate with your account. You can change your browser settings by clicking on the relevant link from the table below.
5. EFFECTIVE DATE OF THE INTERNET SITE PRIVACY POLICY
The Internet Site Privacy Policy is dated The effective date of the Policy will be updated if the entire Policy or specific sections are renewed. The Privacy Policy is published on the Organization’s website (www.socradar.com) and made accessible to relevant individuals upon request.
SOCRadar
Address: 651 N Broad St, Suite 205 Middletown, DE 19709 USA
Phone: +1 (571) 249-4598
Email: [email protected]
Website: www.socradar.com
