
Threat intelligence enriched with External Attack Surface Management, Brand Protection, and Dark Web Radar.
Protect your business from the dangers lurking in the hidden corners of the internet.
Effective threat hunting and threat actor tracking with behavioral analytics.
Discover your assets with a hacker mindset.
Stay ahead of threat actors with actionable intelligence alerts.
Evaluate the security posture of your entire supply network.
Your guide in harnessing the full potential of our platform.
Hear SOCRadar’s impressive achievements from our clients.
Automate and operationalize your security operations.
Consulting and professional services for cybersecurity excellence.
Industry, sector, and region-based in-depth research.
Discover the heartbeat of cyberspace through a collection showcasing the latest incidents.
Discover how XTI empowers organizations to proactively identify, mitigate, and respond to evolving cyber threats.
Register for our live webinars, and watch our on-demand webinars instantly.
Dive deep into the world of cyber threats, advanced analysis techniques, and cutting-edge strategies.
Stay informed and up-to-date on the latest cybersecurity trends.
Explore SOCRadar’s learning experience to fuel your cybersecurity journey with insights that exceed industry standards.
We offer expert-led, and exclusive trainings to help you master the latest in cybersecurity, trusted by over 2,000 top companies.
Scan the dark web to prevent your leaks from turning into real risks.
Instantly access dark web findings about your organization’s assets.
Check if there is anything about you in SOCRadar’s ever-expanding breach database.
Track threat actors and groups by country or industry for effective follow-up.
Explore threat actors’ tactics, techniques, activities, and detailed profiles targeting your industry or region.
All-in-one next-generation tools for investigating everyday events like phishing, malware, account breach, etc.
Power your search with SOCRadar’s IOC Radar.
Let’s get to know each other better.
Broaden your market reach and increase ARR with SOCRadar Extended Threat Intelligence.
Get informed of our upcoming events.
Latest news about our platform, company, and what’s being said about us.
Begin an extraordinary journey in your professional path with SOCRadar.
We’d like to hear from you.
SOCRadar Training Series – Mastering AI in Cybersecurity From Theory to Practice
Resources
[Update] August 13, 2024: “Repossessed: An FBI Operation”
Dispossessor has recently emerged in the ransomware landscape, and it is especially notable for its similarities to the notorious LockBit group. Following an extensive crackdown by global law enforcement agencies, which led to the seizure of LockBit’s primary domains, Dispossessor quickly surfaced, mimicking the structure and content of LockBit.
Dispossessor’s logo
The name “Dispossessor” could be linked to Ursula K. Le Guin’s novel “The Dispossessed,” which explores themes of anarchism, resource scarcity, and socio-political upheaval. The novel presents a dichotomy between a society devoid of personal property and one rich in resources but rife with inequality and competition.
Such references are common among ransomware and extortion groups that engage in million-dollar thefts and extortions but still see themselves on the morally high ground.
In February 2024, Dispossessor made a bold entrance into the dark web, announcing the availability of previously leaked data for download and potential sale. These announcements appeared across multiple forums and markets, including BreachForums and XSS as stated by SentinelOne.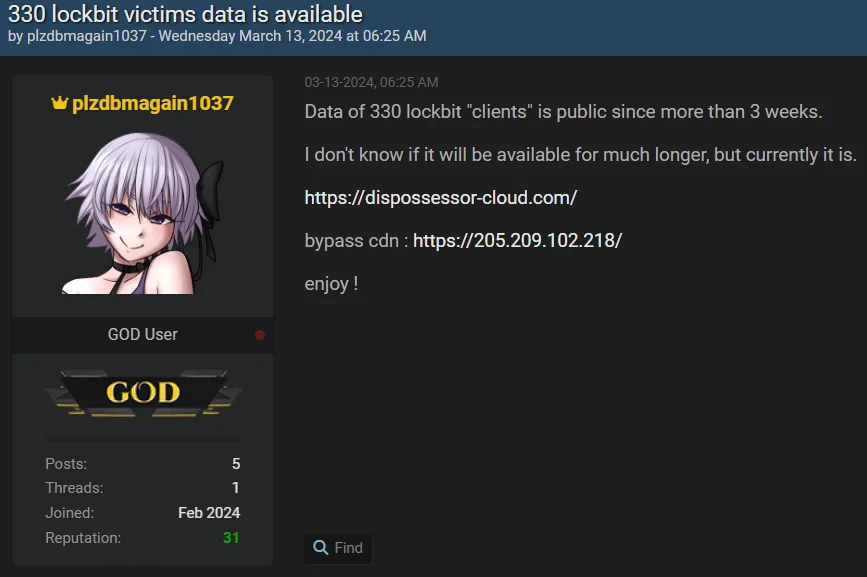
Post about Dispossessor in a hacker forum
The timing was particularly notable, as it followed closely after Operation Cronos, a coordinated effort led by the FBI to shut down LockBit’s operations. This operation saw multiple domains owned by LockBit seized, disabling access to their affiliate panel and other critical infrastructure.
Dispossessor’s website bears a striking resemblance to the original LockBit site. The layout, color scheme, and typefaces are nearly identical, suggesting either a rebranding effort by the same operators or a new group leveraging LockBit’s infrastructure. Content analysis reveals that many posts from the original LockBit site have been mirrored on Dispossessor’s platform on their first days, maintaining the exact publication dates and details.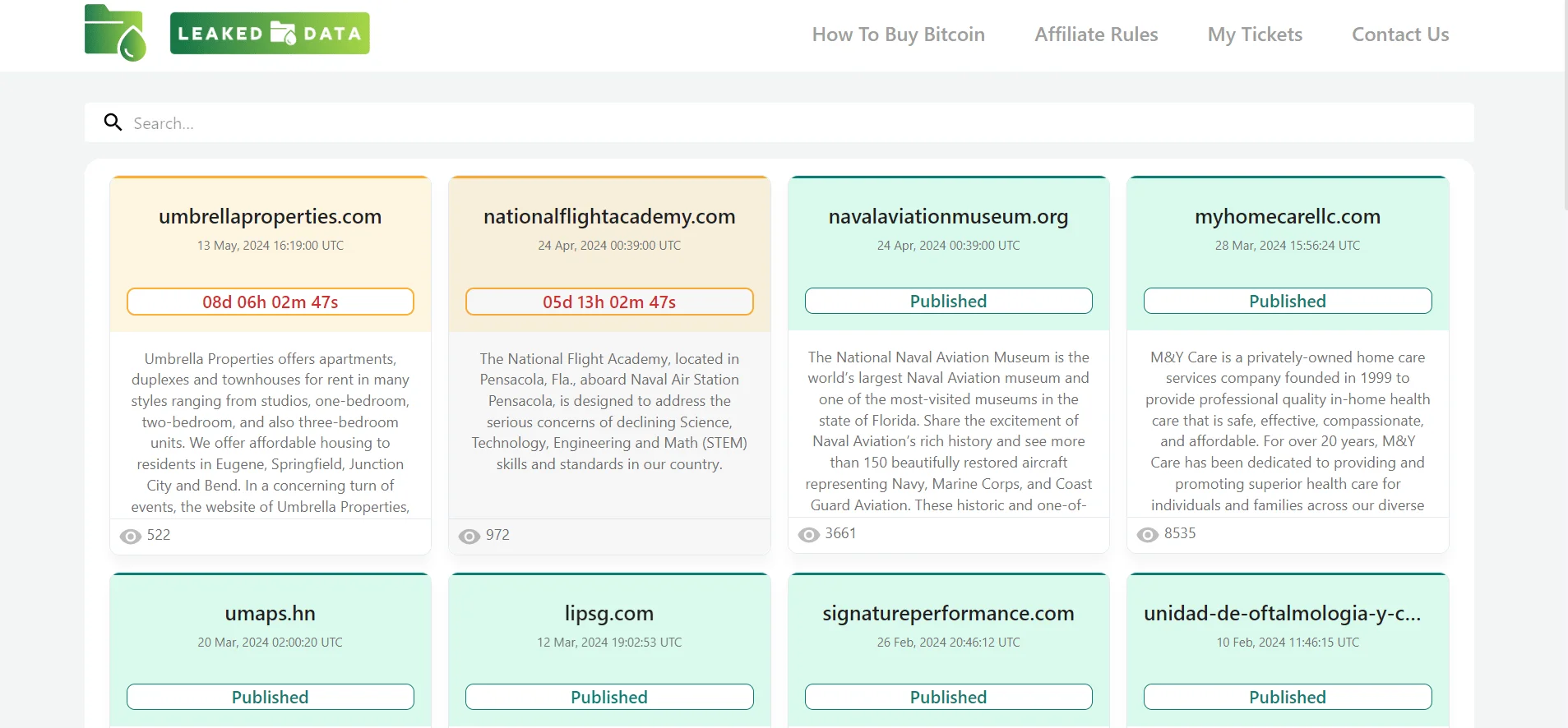
Dashboard of Dispossessor’s surface web leak site
Users on the hacking forums also mentioned a new site named Dispossessor, noting its similarity to the original LockBit site.
Dispossessor follows the Ransomware-as-a-Service (RaaS) model, similar to LockBit. This approach allows RaaS groups to distribute ransomware through affiliates, who then execute attacks on various targets. The decentralized nature of this model makes it challenging for law enforcement to completely dismantle their operations.
However, Dispossessor does not appear to possess ransomware capabilities; instead, it functions more accurately as a data broker. Since no instances of their ransomware have been observed, it is clear that they are primarily publishing data leaks from other groups, including those that are now defunct or have been shut down. This makes them opportunistic threat actors.
As firstly stated by @ransomfeednews in X, “We have noticed that there is a lot of talk about the alleged new ransomware group #dispossessor; we did some checking and analyzed the situation. In light of everything, from our point of view it is not #ransomware, but a group of scoundrels trying to monetize (on nothing) using the claims of other groups.”
A similar situation was observed with Ransomhub concerning the Change Healthcare data. Dispossessor relies on affiliates from other ransomware groups who have already acquired or stolen data. However, their latest victim portfolio has diversified from those targeted by LockBit or other groups, and they are actively seeking “red teamers” on hacker forums to collaborate with. Therefore, it could be expected that something may change.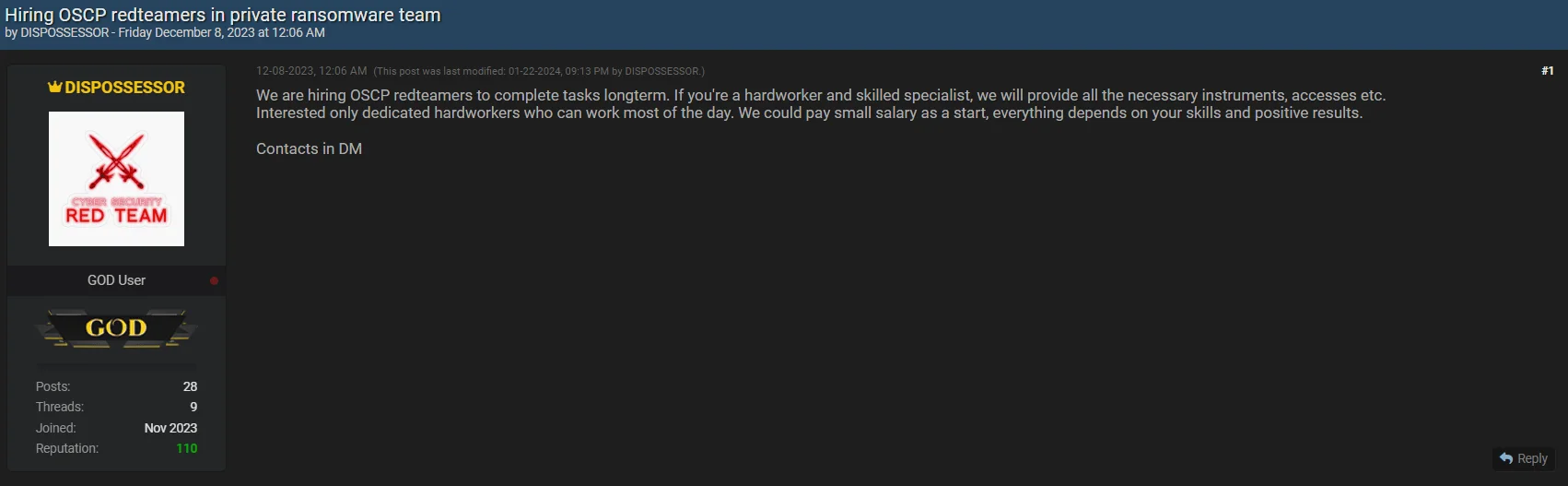
Group was looking for red teamers in late 2023
When we look at the number of victims, we can see that it contains 17 pages and around 300 company names, but the majority of them consist of victims previously listed in groups such as LockBit, Cl0p or Snatch.
According to their data leak site, Dispossessor’s affiliate program is notably inclusive, welcoming participants regardless of their location, language, age, or religion. The program prioritizes cohesive and experienced teams of “pen testers” and access providers -initial access brokers-offering a transparent process where affiliates can control communication with victims.
Affiliates using Dispossessor’s platform have access to a comprehensive toolkit designed to maximize the impact of their attacks. Key features include an admin panel on the Tor network, secure communication channels, automatic decryption tools, and StealBit stealer, which enables the theft of valuable data. The platform also supports various operating systems and architectures, including Windows, ESXi, and multiple Linux distributions.
Dispossessor’s Affiliate Program Rules
Dispossessor’s rules on their data leak site outline a structured affiliate program. Affiliates are expected to actively work with the software package provided by Dispossessor and adhere to strict guidelines to maintain operational security. Key rules include:
Dispossessor’s emphasis on operational security extends to a deposit requirement for new affiliates. Prospective members must deposit 1 Bitcoin, which serves as an advance payment for future ransom shares. This requirement is intended to weed out insecure novices, law enforcement agents, journalists, and competitors.
The FBI recently scored a big win against the Dispossessor ransomware group by disrupting their operations and seizing several of their servers. This group had been on the FBI’s radar for months, and this latest move is part of a larger effort to take down their network and bring those involved to justice.
The FBI explained that this disruption came after a long investigation focused on the servers Dispossessor used to launch their attacks. By taking control of these servers, law enforcement has seriously weakened the group’s ability to lock up and steal data from their victims. For now, this should put a dent in Dispossessor’s operations.
Seizure announcement on the Dispossessor’s leak site
This action is just one piece of a broader strategy to fight ransomware, involving teamwork between international partners and private companies. The takedown sends a clear message to cybercriminals and shows the power of working together to combat these threats.
That said, this might not be the end of Dispossessor. Ransomware groups are known for bouncing back, often with new tricks up their sleeves. So, it’s important for organizations to stay alert and keep strengthening their defenses against potential attacks.
Dispossessor’s emergence as a significant player in the cyber threat landscape, closely following the crackdown on LockBit, highlights the dynamic and adaptive nature of cybercriminal activities. Their operational tactics, mimicking the Ransomware-as-a-Service model while primarily functioning as data brokers, present a unique challenge for cybersecurity experts and law enforcement agencies.
Therefore, focusing on general ransomware defense strategies with data protection in mind is crucial for robust cybersecurity resilience.
SOCRadar provides proactive threat monitoring and intelligence solutions to strengthen your organization’s security posture against ransomware attacks. With our platform, you can proactively search for threat actors, gain insights into their tactics and vulnerabilities, and take preemptive measures to protect your assets.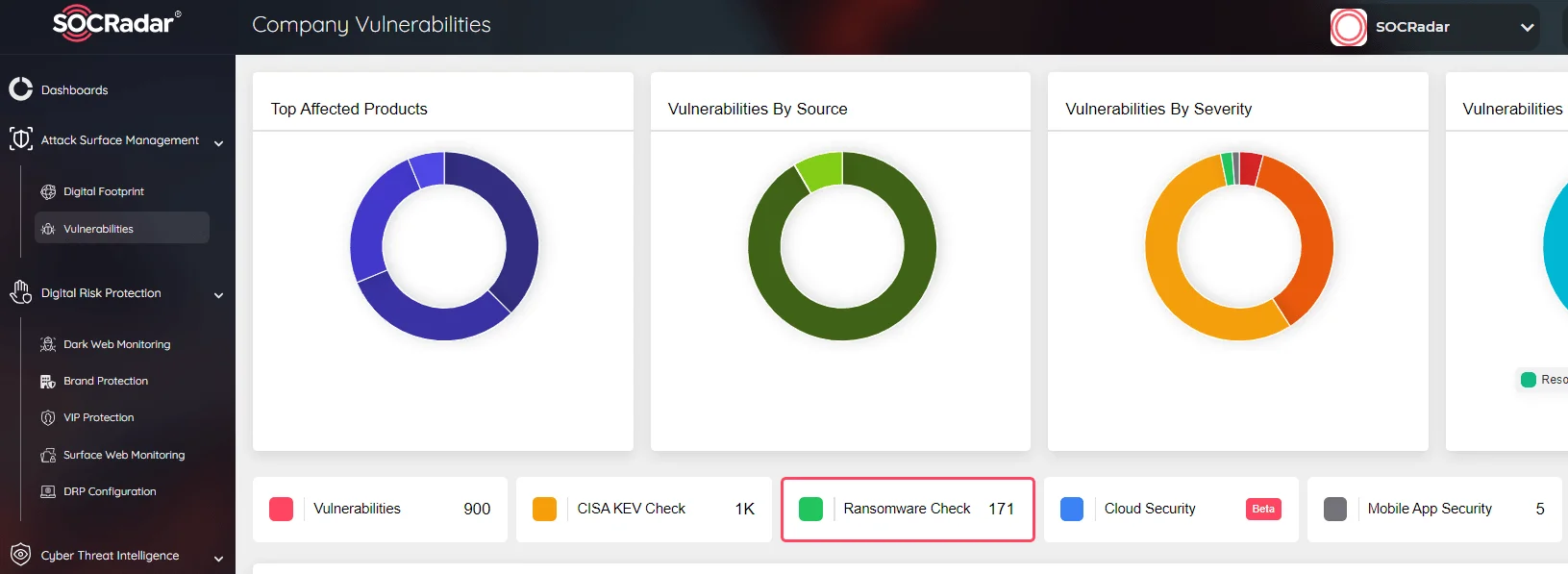
SOCRadar Attack Surface Management, Ransomware Check
Our Attack Surface Management module offers continuous monitoring of potential attack vectors, ensuring timely alerts about suspicious activity. This proactive approach enables swift responses to threats, enhancing overall cybersecurity defenses. Integrating SOCRadar into your cybersecurity framework adds an extra layer of protection against ransomware and other threats.
Subscribe to our newsletter and stay updated on the latest insights!
PROTECTION OF PERSONAL DATA COOKIE POLICY FOR THE INTERNET SITE
Protecting your personal data is one of the core principles of our organization, SOCRadar, which operates the internet site (www.socradar.com). This Cookie Usage Policy (“Policy”) explains the types of cookies used and the conditions under which they are used to all website visitors and users.
Cookies are small text files stored on your computer or mobile device by the websites you visit.
Cookies are commonly used to provide you with a personalized experience while using a website, enhance the services offered, and improve your overall browsing experience, contributing to ease of use while navigating a website. If you prefer not to use cookies, you can delete or block them through your browser settings. However, please be aware that this may affect your usage of our website. Unless you change your cookie settings in your browser, we will assume that you accept the use of cookies on this site.
1. WHAT KIND OF DATA IS PROCESSED IN COOKIES?
Cookies on websites collect data related to your browsing and usage preferences on the device you use to visit the site, depending on their type. This data includes information about the pages you access, the services and products you explore, your preferred language choice, and other preferences.
2. WHAT ARE COOKIES AND WHAT ARE THEIR PURPOSES?
Cookies are small text files stored on your device or web server by the websites you visit through your browsers. These small text files, containing your preferred language and other settings, help us remember your preferences on your next visit and assist us in making improvements to our services to enhance your experience on the site. This way, you can have a better and more personalized user experience on your next visit.
The main purposes of using cookies on our Internet Site are as follows:
3. TYPES OF COOKIES USED ON OUR INTERNET SITE 3.1. Session Cookies
Session cookies ensure the smooth operation of the internet site during your visit. They are used for purposes such as ensuring the security and continuity of our sites and your visits. Session cookies are temporary cookies and are deleted when you close your browser; they are not permanent.
3.2. Persistent Cookies
These cookies are used to remember your preferences and are stored on your device through browsers. Persistent cookies remain stored on your device even after you close your browser or restart your computer. These cookies are stored in your browser’s subfolders until deleted from your browser’s settings. Some types of persistent cookies can be used to provide personalized recommendations based on your usage purposes.
With persistent cookies, when you revisit our website with the same device, the website checks if a cookie created by our website exists on your device. If so, it is understood that you have visited the site before, and the content to be presented to you is determined accordingly, offering you a better service.
3.3. Mandatory/Technical Cookies
Mandatory cookies are essential for the proper functioning of the visited internet site. The purpose of these cookies is to provide necessary services by ensuring the operation of the site. For example, they allow access to secure sections of the internet site, use of its features, and navigation.
3.4. Analytical Cookies
These cookies gather information about how the website is used, the frequency and number of visits, and show how visitors navigate to the site. The purpose of using these cookies is to improve the operation of the site, increase its performance, and determine general trend directions. They do not contain data that can identify visitors. For example, they show the number of error messages displayed or the most visited pages.
3.5. Functional Cookies
Functional cookies remember the choices made by visitors within the site and recall them during the next visit. The purpose of these cookies is to provide ease of use to visitors. For example, they prevent the need to re-enter the user’s password on each page visited by the site user.
3.6. Targeting/Advertising Cookies
They measure the effectiveness of advertisements shown to visitors and calculate how many times ads are displayed. The purpose of these cookies is to present personalized advertisements to visitors based on their interests.
Similarly, they determine the specific interests of visitors’ navigation and present appropriate content. For example, they prevent the same advertisement from being shown again to the visitor in a short period.
4. HOW TO MANAGE COOKIE PREFERENCES?
To change your preferences regarding the use of cookies, block or delete cookies, you only need to change your browser settings.
Many browsers offer options to accept or reject cookies, only accept certain types of cookies, or receive notifications from the browser when a website requests to store cookies on your device.
Also, it is possible to delete previously saved cookies from your browser.
If you disable or reject cookies, you may need to manually adjust some preferences, and certain features and services on the website may not work properly as we will not be able to recognize and associate with your account. You can change your browser settings by clicking on the relevant link from the table below.
5. EFFECTIVE DATE OF THE INTERNET SITE PRIVACY POLICY
The Internet Site Privacy Policy is dated The effective date of the Policy will be updated if the entire Policy or specific sections are renewed. The Privacy Policy is published on the Organization’s website (www.socradar.com) and made accessible to relevant individuals upon request.
SOCRadar
Address: 651 N Broad St, Suite 205 Middletown, DE 19709 USA
Phone: +1 (571) 249-4598
Email: [email protected]
Website: www.socradar.com
