
Threat intelligence enriched with External Attack Surface Management, Brand Protection, and Dark Web Radar.
Protect your business from the dangers lurking in the hidden corners of the internet.
Effective threat hunting and threat actor tracking with behavioral analytics.
Discover your assets with a hacker mindset.
Stay ahead of threat actors with actionable intelligence alerts.
Evaluate the security posture of your entire supply network.
Your guide in harnessing the full potential of our platform.
Hear SOCRadar’s impressive achievements from our clients.
Automate and operationalize your security operations.
Consulting and professional services for cybersecurity excellence.
Industry, sector, and region-based in-depth research.
Discover the heartbeat of cyberspace through a collection showcasing the latest incidents.
Discover how XTI empowers organizations to proactively identify, mitigate, and respond to evolving cyber threats.
Register for our live webinars, and watch our on-demand webinars instantly.
Dive deep into the world of cyber threats, advanced analysis techniques, and cutting-edge strategies.
Stay informed and up-to-date on the latest cybersecurity trends.
Explore SOCRadar’s learning experience to fuel your cybersecurity journey with insights that exceed industry standards.
We offer expert-led, and exclusive trainings to help you master the latest in cybersecurity, trusted by over 2,000 top companies.
Scan the dark web to prevent your leaks from turning into real risks.
Instantly access dark web findings about your organization’s assets.
Check if there is anything about you in SOCRadar’s ever-expanding breach database.
Track threat actors and groups by country or industry for effective follow-up.
Explore threat actors’ tactics, techniques, activities, and detailed profiles targeting your industry or region.
All-in-one next-generation tools for investigating everyday events like phishing, malware, account breach, etc.
Power your search with SOCRadar’s IOC Radar.
Let’s get to know each other better.
Broaden your market reach and increase ARR with SOCRadar Extended Threat Intelligence.
Get informed of our upcoming events.
Latest news about our platform, company, and what’s being said about us.
Begin an extraordinary journey in your professional path with SOCRadar.
We’d like to hear from you.
SOCRadar Training Series – Mastering AI in Cybersecurity From Theory to Practice
Resources
Originating in the latter part of 2023, this Ransomware-as-a-Service (RaaS) operation has drawn attention due to its technical lineage and operational tactics resembling those of the notorious Hive ransomware group. With law enforcement agencies previously disrupting Hive, Hunters International’s rise just after the operation underscores the persistent and adaptive nature of cybercriminal networks.
Hunters International’s logo
Hunters International emerged in the cyber landscape around the time of the disruption of the Hive ransomware group by law enforcement agencies. This new group, detected in Q3 of 2023, exhibited significant technical overlap with Hive, suggesting an evolution or offshoot of the dismantled operation. The transition highlights the adaptive strategies of cybercriminal networks, which evolve to sustain their malicious activities despite law enforcement efforts. Hunters International’s initiation and operational blueprint reflect a continued threat in the realm of cyber extortion and data theft.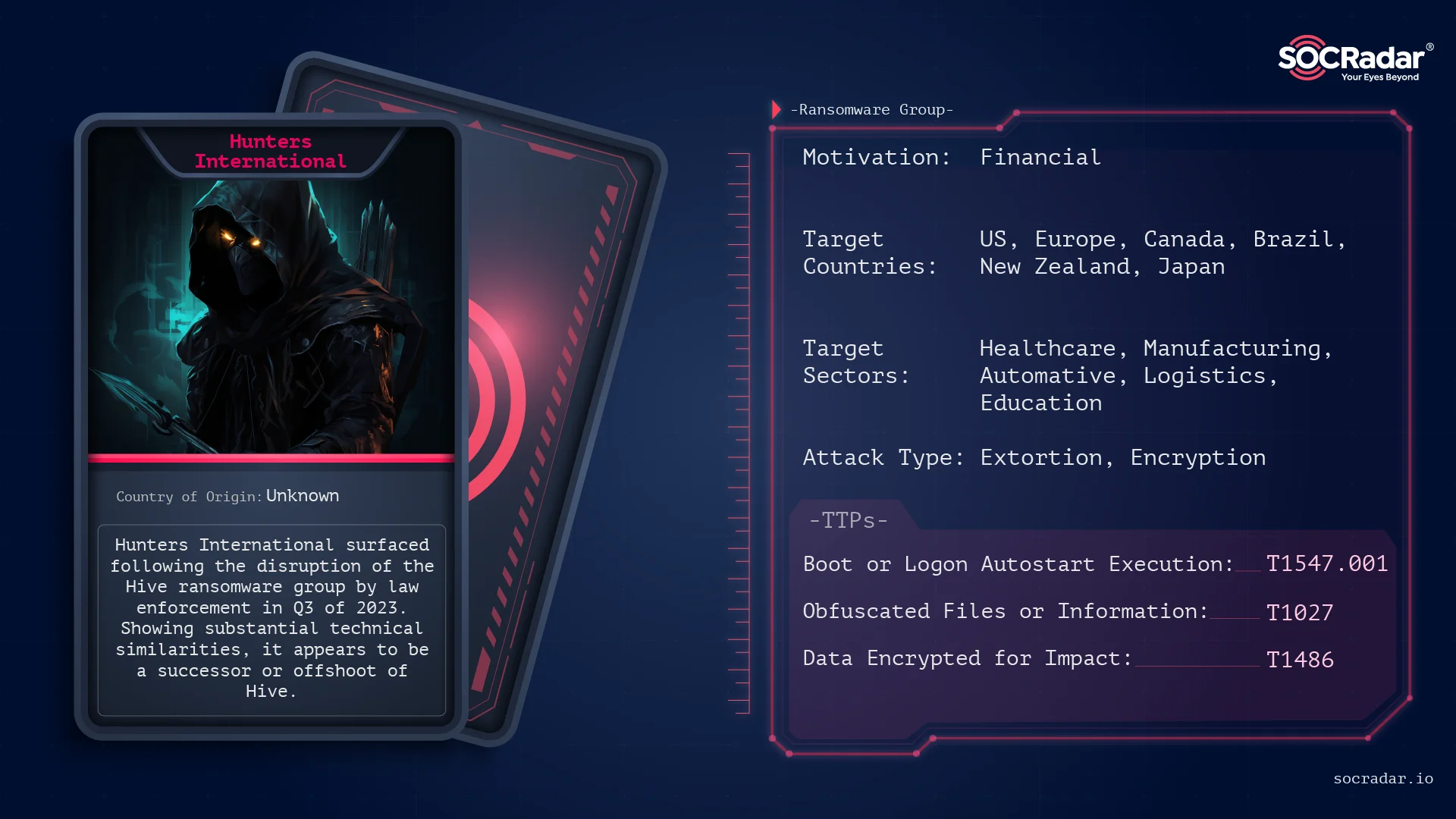
Threat Actor Card for Hunters International
Once again, their techniques and ransomware strain reveals a significant overlap with the Hive ransomware, indicating a shared lineage or possible transfer of technology. This connection suggests that Hunters International have inherited or adapted Hive’s encryption techniques and operational strategies.
FBI’s takedown notice on Hive’s websites.
In January 2023, a coalition involving the US Department of Justice, FBI, Secret Service, Europol, and European agencies targeted the Hive ransomware group. This notorious collective, responsible for extorting over $100 million from more than 1,500 global victims since June 2021, including healthcare, education, and financial sectors, saw two of their extortion and data leak sites seized. These actions displayed international law enforcement’s commitment to dismantling cyber threats and protecting vulnerable sectors from ransomware attacks.
The dismantling of Hive’s network followed a seven-month undercover FBI operation, granting them network access and enabling the provision of decryption keys to over 300 entities, averting about $130 million in potential ransom payments. Additionally, 1,000 more keys were given to previous victims. Despite no arrests, the operation significantly impacted Hive’s operations, highlighting the challenges law enforcement faces with cybercriminals often based in jurisdictions less cooperative with international law enforcement efforts. This raises questions about the future actions of such disrupted groups.
Around these developments, a report from Bitdefender even suggested that Hive’s leaders strategically chose to end their operations, transferred assets to Hunters International.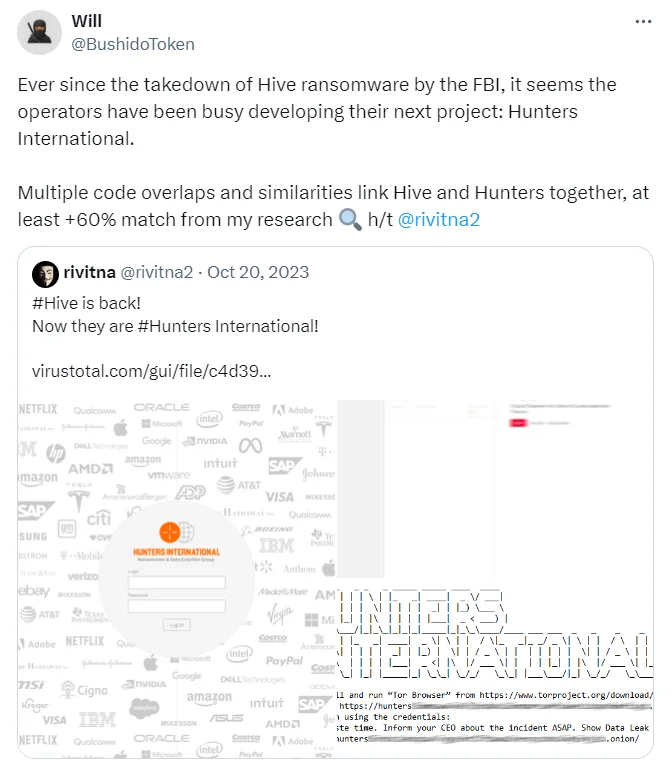
Tweets from researchers, @rivitna2 and @BushidoToken
In fact, security researchers at X (formerly Twitter) stated that Hunters had approximately 60% code similarity when it was first released.
But upon these allegations Hunters International stated that they are not simply a new version of Hive but an independent entity that took over Hive’s source code and infrastructure. Their main operational focus is on stealing data rather than encrypting it, distinguishing their approach from Hive’s.
Their explanation seems acceptable. As analyzed by Bitdefender, the group’s focus significantly leans towards stealing data, as evidenced by all known victims experiencing data exfiltration, whereas not every victim’s data was encrypted. Hunters International seems to have customized Hive’s ransomware to enhance simplicity and efficiency.
By reducing command-line options and optimizing encryption key management, they’ve made their malware less verbose and easier to use for operatives. The switch to Rust, mirroring trends in sophisticated ransomware development, aids in evading detection and facilitates faster encryption. Their unique approach embeds encryption keys within the encrypted files, a method aimed at streamlining the decryption process for victims who pay the ransom while also complicating security professionals’ efforts to counteract the malware.
Hunters International has targeted a diverse array of industries worldwide, demonstrating a global reach with a strategic focus on maximizing impact and ransom potential. Their victims span across healthcare, automotive, manufacturing, logistics, financial, educational, and food sectors, indicating a non-discriminatory approach aimed at exploiting any vulnerable entity.
Group has been very busy, attacking a lot of different organizations all over the world. Most of their targets are in the United States, but they didn’t stop there; they went after companies and organizations in Europe, Canada, Brazil, and even as far as New Zealand and Japan. It’s like they’re casting a wide net to see what they can catch, without really caring who the victim is.
They’re not picky about who they attack either. Whether it’s an energy company, a hospital, a school, or even a zoo, they’re all fair game to this group. It seems like they’re just looking for any opportunity to make money, going after those who might not have strong protection against cyber attacks or who would really feel the pressure to pay up if their data were taken or locked up.
This wide-ranging victimology underscores the group’s opportunistic nature and its capacity to adapt and penetrate various sectors, posing a significant threat to organizations of all sizes and functions globally. Because financial income is a priority, this wide target audience is normal, especially in groups working with the RaaS model.
The later investigations into Hunters International led to the exposure of its data leak site’s identity, revealing potential ties to Nigeria through domain registrations and email addresses associated with the group. On January 22, 2024, Hunters International unveiled a non-dark web version of their leak site under the same name.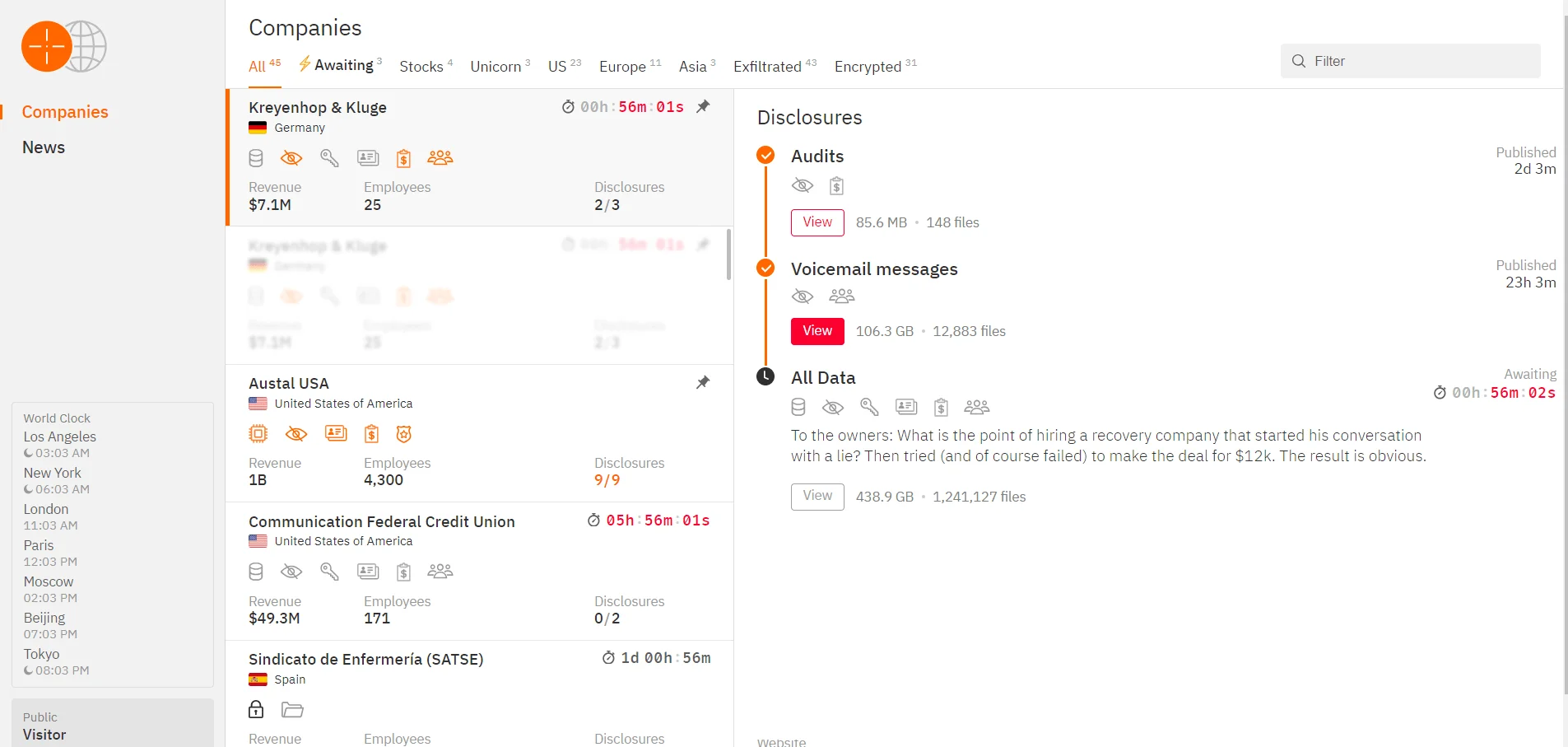
Hunters International’s surface web data leak site
As researcher Krishnan states, they brought back a website that hadn’t been used since 2021, using a fake name to hide who they really are and make it harder to find them. When digging into it, they found email addresses that might connect the group to Nigeria. But, it’s possible these emails are just tricks meant to lead people on the wrong path. This mix of real and fake identities shows how hard it is to figure out who is behind cybercrimes. It shows how clever and complex groups like Hunters International are. They’re very careful to keep their identities secret and use tricky methods that show they operate all over the world.
The impact of Hunters International’s ransomware attacks is multifaceted like many ransomware incidents, causing significant data breaches, financial losses, and reputational damage to affected organizations. In response, cybersecurity experts recommend a proactive and comprehensive approach to defense, including regular data backups, employee training on phishing detection, and the implementation of robust cybersecurity frameworks to mitigate risks. Organizations are also advised to engage in threat intelligence sharing and collaborate with law enforcement to enhance their resilience against such evolving cyber threats.
The emergence and activities of Hunters International exemplify the persistent and evolving nature of cyber threats in the digital age. Despite significant efforts to dismantle ransomware operations, groups like Hunters International continue to pose substantial risks to global cybersecurity. Their sophisticated tactics, global reach, and ability to adapt underscore the importance of sustained vigilance, proactive defense strategies, and international cooperation among cybersecurity communities to mitigate these threats effectively.
The SOCRadar Cyber Threat Intelligence suite provides tools to help detect and prevent ransomware with its Threat Hunting feature, allowing users to search billions of records for Indicators of Compromise (IoCs) and gather important data. This data can be integrated into SOAR systems via a Restful API, enabling the creation of custom feeds for SIEM systems, Firewalls, and EDR platforms to improve defense against ransomware. SOCRadar also includes a Ransomware Check in its Attack Surface Management, allowing easy integration of these feeds into security setups to protect against threats from new malicious URLs.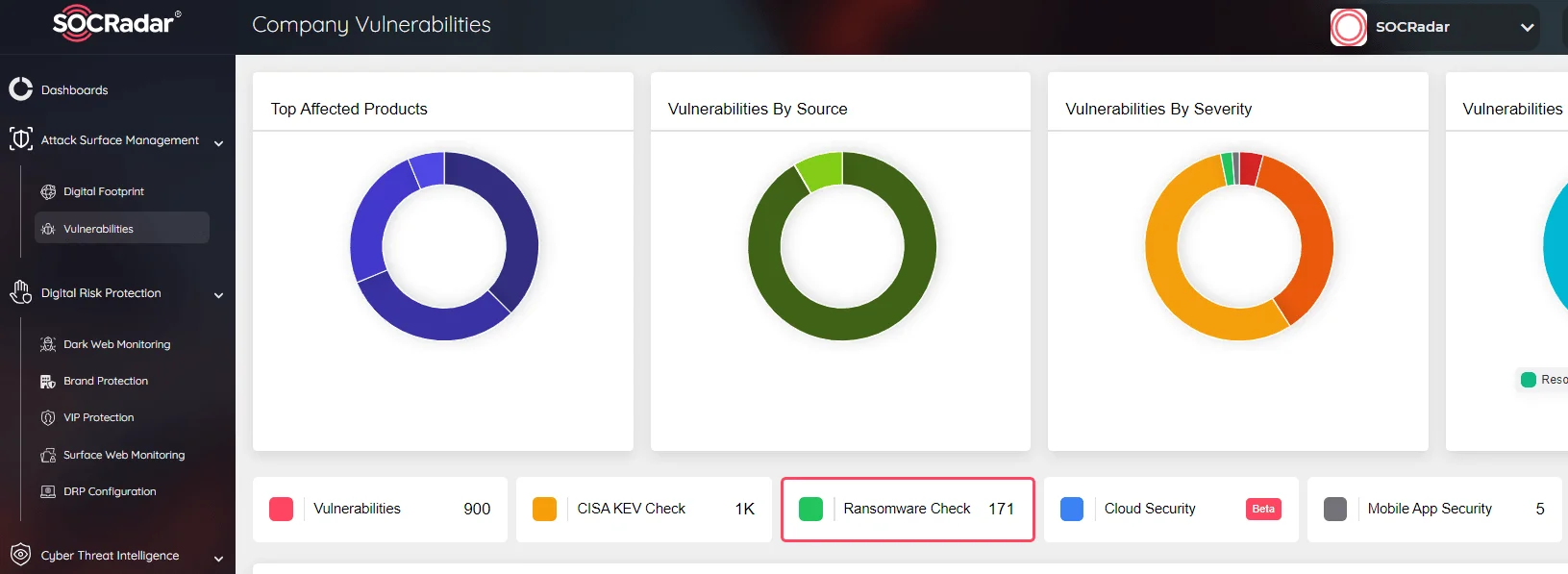
SOCRadar Attack Surface Management, Ransomware Check
SOCRadar continuously enhances its platform to address your security needs and protect against the evolving tactics of cybercriminals. We encourage you to explore our platform, available at no cost, and share your feedback to strengthen your digital security.
Subscribe to our newsletter and stay updated on the latest insights!
PROTECTION OF PERSONAL DATA COOKIE POLICY FOR THE INTERNET SITE
Protecting your personal data is one of the core principles of our organization, SOCRadar, which operates the internet site (www.socradar.com). This Cookie Usage Policy (“Policy”) explains the types of cookies used and the conditions under which they are used to all website visitors and users.
Cookies are small text files stored on your computer or mobile device by the websites you visit.
Cookies are commonly used to provide you with a personalized experience while using a website, enhance the services offered, and improve your overall browsing experience, contributing to ease of use while navigating a website. If you prefer not to use cookies, you can delete or block them through your browser settings. However, please be aware that this may affect your usage of our website. Unless you change your cookie settings in your browser, we will assume that you accept the use of cookies on this site.
1. WHAT KIND OF DATA IS PROCESSED IN COOKIES?
Cookies on websites collect data related to your browsing and usage preferences on the device you use to visit the site, depending on their type. This data includes information about the pages you access, the services and products you explore, your preferred language choice, and other preferences.
2. WHAT ARE COOKIES AND WHAT ARE THEIR PURPOSES?
Cookies are small text files stored on your device or web server by the websites you visit through your browsers. These small text files, containing your preferred language and other settings, help us remember your preferences on your next visit and assist us in making improvements to our services to enhance your experience on the site. This way, you can have a better and more personalized user experience on your next visit.
The main purposes of using cookies on our Internet Site are as follows:
3. TYPES OF COOKIES USED ON OUR INTERNET SITE 3.1. Session Cookies
Session cookies ensure the smooth operation of the internet site during your visit. They are used for purposes such as ensuring the security and continuity of our sites and your visits. Session cookies are temporary cookies and are deleted when you close your browser; they are not permanent.
3.2. Persistent Cookies
These cookies are used to remember your preferences and are stored on your device through browsers. Persistent cookies remain stored on your device even after you close your browser or restart your computer. These cookies are stored in your browser’s subfolders until deleted from your browser’s settings. Some types of persistent cookies can be used to provide personalized recommendations based on your usage purposes.
With persistent cookies, when you revisit our website with the same device, the website checks if a cookie created by our website exists on your device. If so, it is understood that you have visited the site before, and the content to be presented to you is determined accordingly, offering you a better service.
3.3. Mandatory/Technical Cookies
Mandatory cookies are essential for the proper functioning of the visited internet site. The purpose of these cookies is to provide necessary services by ensuring the operation of the site. For example, they allow access to secure sections of the internet site, use of its features, and navigation.
3.4. Analytical Cookies
These cookies gather information about how the website is used, the frequency and number of visits, and show how visitors navigate to the site. The purpose of using these cookies is to improve the operation of the site, increase its performance, and determine general trend directions. They do not contain data that can identify visitors. For example, they show the number of error messages displayed or the most visited pages.
3.5. Functional Cookies
Functional cookies remember the choices made by visitors within the site and recall them during the next visit. The purpose of these cookies is to provide ease of use to visitors. For example, they prevent the need to re-enter the user’s password on each page visited by the site user.
3.6. Targeting/Advertising Cookies
They measure the effectiveness of advertisements shown to visitors and calculate how many times ads are displayed. The purpose of these cookies is to present personalized advertisements to visitors based on their interests.
Similarly, they determine the specific interests of visitors’ navigation and present appropriate content. For example, they prevent the same advertisement from being shown again to the visitor in a short period.
4. HOW TO MANAGE COOKIE PREFERENCES?
To change your preferences regarding the use of cookies, block or delete cookies, you only need to change your browser settings.
Many browsers offer options to accept or reject cookies, only accept certain types of cookies, or receive notifications from the browser when a website requests to store cookies on your device.
Also, it is possible to delete previously saved cookies from your browser.
If you disable or reject cookies, you may need to manually adjust some preferences, and certain features and services on the website may not work properly as we will not be able to recognize and associate with your account. You can change your browser settings by clicking on the relevant link from the table below.
5. EFFECTIVE DATE OF THE INTERNET SITE PRIVACY POLICY
The Internet Site Privacy Policy is dated The effective date of the Policy will be updated if the entire Policy or specific sections are renewed. The Privacy Policy is published on the Organization’s website (www.socradar.com) and made accessible to relevant individuals upon request.
SOCRadar
Address: 651 N Broad St, Suite 205 Middletown, DE 19709 USA
Phone: +1 (571) 249-4598
Email: [email protected]
Website: www.socradar.com
