
Threat intelligence enriched with External Attack Surface Management, Brand Protection, and Dark Web Radar.
Protect your business from the dangers lurking in the hidden corners of the internet.
Effective threat hunting and threat actor tracking with behavioral analytics.
Discover your assets with a hacker mindset.
Stay ahead of threat actors with actionable intelligence alerts.
Evaluate the security posture of your entire supply network.
Your guide in harnessing the full potential of our platform.
Hear SOCRadar’s impressive achievements from our clients.
Automate and operationalize your security operations.
Consulting and professional services for cybersecurity excellence.
Industry, sector, and region-based in-depth research.
Discover the heartbeat of cyberspace through a collection showcasing the latest incidents.
Discover how XTI empowers organizations to proactively identify, mitigate, and respond to evolving cyber threats.
Register for our live webinars, and watch our on-demand webinars instantly.
Dive deep into the world of cyber threats, advanced analysis techniques, and cutting-edge strategies.
Stay informed and up-to-date on the latest cybersecurity trends.
Explore SOCRadar’s learning experience to fuel your cybersecurity journey with insights that exceed industry standards.
We offer expert-led, and exclusive trainings to help you master the latest in cybersecurity, trusted by over 2,000 top companies.
Scan the dark web to prevent your leaks from turning into real risks.
Instantly access dark web findings about your organization’s assets.
Check if there is anything about you in SOCRadar’s ever-expanding breach database.
Track threat actors and groups by country or industry for effective follow-up.
Explore threat actors’ tactics, techniques, activities, and detailed profiles targeting your industry or region.
All-in-one next-generation tools for investigating everyday events like phishing, malware, account breach, etc.
Power your search with SOCRadar’s IOC Radar.
Let’s get to know each other better.
Broaden your market reach and increase ARR with SOCRadar Extended Threat Intelligence.
Get informed of our upcoming events.
Latest news about our platform, company, and what’s being said about us.
Begin an extraordinary journey in your professional path with SOCRadar.
We’d like to hear from you.
SOCRadar Training Series – Mastering AI in Cybersecurity From Theory to Practice
Resources
In late 2022, 4 ransomware strains were discovered that are derived from Conti‘s leaked ransomware strain. One of them was Meow ransomware. The operation of this crypto-ransomware was observed from late August to the first half of September 2022 and persisted until February 2023. In March 2023, a free decryptor for the Meow ransomware was released, leading to the cessation of their operation.
At the time the incident occurred, Kaspersky suggested that a modified Conti strain was likely employed to encrypt 257 victims, with 14 of them paying the attackers to regain access to their data. The private keys used for decryption were generated between November 13, 2022, and February 5, 2023, indicating the timeframe of the attacks.
A group named Meow is still active, and has made a relatively rapid entry into 2024 and has nine victims in 2024 so far. Although it does not seem to be a group that does not work with the RaaS model, they have three listed victims in March 2024 alone, and the institutions they target are not small targets.
Illustrated with Bing Image Creator
With no recent instances of sample encryptors being detected, the latest iteration of Meow ransomware could potentially operate solely as an extortion group, assuming it is the same entity. Therefore, we can’t state definitively whether Meow, the group still active, is a direct continuation of the previous operation -MeowCorps.
However, much like the Snatch group, they are probably adept hackers but lack the skills in malware development. Their ransomware was compromised after the release of the decryptor, but they haven’t managed to create a more sophisticated strain.
All recent victims listed on their leak site mention data extraction without any mention of encryption. There hasn’t been any indication of ransomware being employed in their operations, and their website is currently named Meow Leaks.
A thread in the XSS forum
The only aspect raising our doubts is that the Conti-based Meow encryptor targeted many Russian organizations initially. Consequently, some sources labeled them as an anti-Russian extortion group. However, their current choice of victims differs significantly from this characterization.
Initially identified in August 2022, the Meow ransomware, associated with the Conti v2 variant, disappeared for a while after March of 2023, but a similar in name group surfaced in late 2023 and they remain highly active in 2024. They maintain a data leak site where they list 24 victims. Its dark web presence displays a limited roster of victims, but only those who haven’t paid the ransom are shown.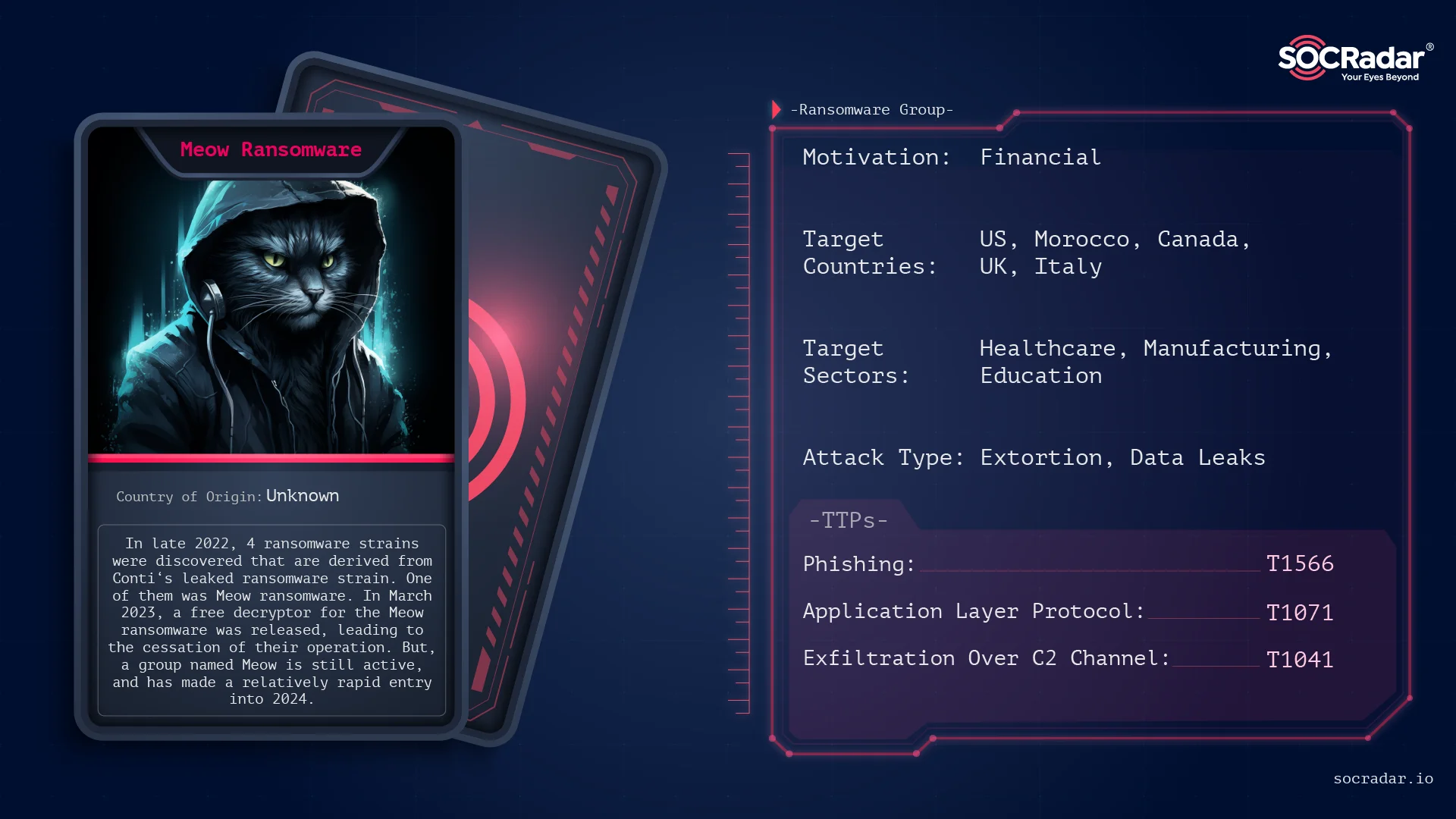
Threat Actor Card for Meow Ransomware
Once operating under different names like MeowCorp, MeowLeaks, or just Meow, it employed the ChaCha20 algorithm to encrypt data on compromised servers. Victims are then instructed to contact the extortionists through email or Telegram to receive instructions on paying the ransom and recovering their files. The title of the ransom note included the phrase “MEOW! MEOW! MEOW!” and “meowcorp2022” reiterated in the login credentials as of their initial ransomware strain in 2022.
Compared to the old Meow, victim preferences are quite different. Their country target list is not extensive; the vast majority of their targets are in the US, with 17 attacks recorded. Meanwhile, Morocco has experienced 2 attacks, while Canada, UK, Italy, Nigeria, and Singapore each have 1 victim.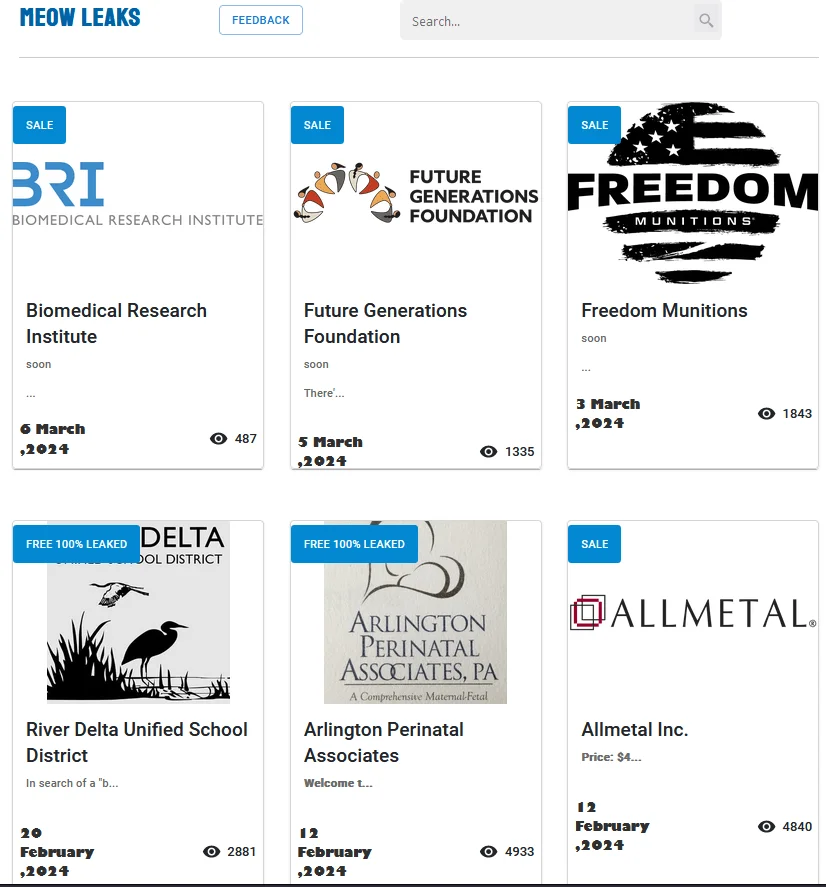
Meow Leaks Home Page
They are likely selecting targets with sensitive data since they cannot rely on encryption for extorting payment. Industries such as Healthcare and Medical Research are frequently targeted in their attacks.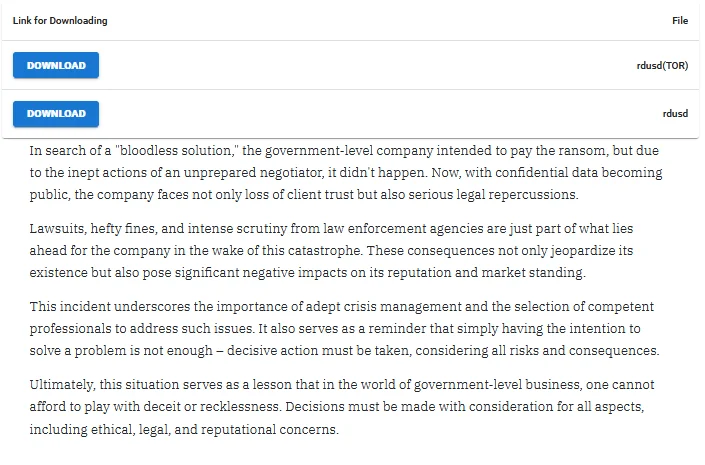
Victim “shaming” for River Delta Unified School District
They posted the above statement on their data leak site while disclosing the data of a victim who indicated intentions to pay. They explained that the purported reason for the failed agreement was an “unprepared ransomware negotiator.”
Alleged data sale of a victim company
Based on the content of the data, a price is assigned, and potential buyers are invited to reach out to them.
Contacting with Meow Project
On their data leak sites, only the contact section exists, excluding victim listings.
They sell certain data to multiple buyers but do not provide updates on whether the purchase(s) have been completed. The price range spans from approximately $2,999 to $60,000.
Let’s examine the period when Meow ransomware was capable of encrypting data with ransomware. As stated before, a variant stemming from leaked code of Conti-2 Ransomware encrypted data on compromised servers using the ChaCha20 algorithm. It demanded ransom payments from victims through various communication channels such as email or Telegram.
The ransomware was initially observed towards the end of August and the beginning of September 2022 and remained active until February 2023. The encrypted files bore the “.MEOW” extension, and the ransom note was named “readme.txt.”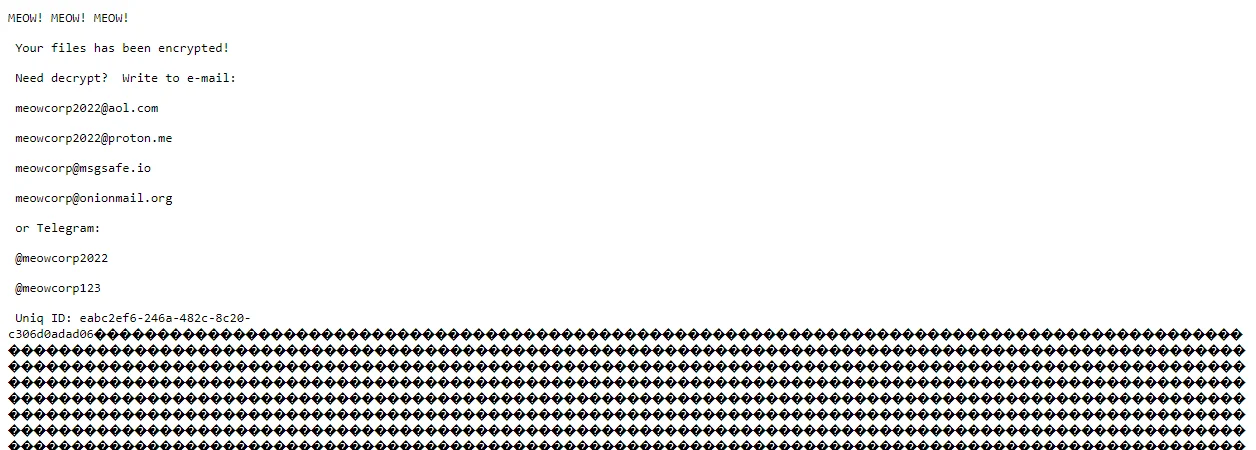
Meow Ransomware note (Source)
The ransom note, marked with the repeated phrase “MEOW! MEOW! MEOW!”, instructed victims to contact the extortionists via specified email addresses and Telegram accounts to negotiate ransom payments and retrieve their encrypted files.
Meow ransomware spread through various means, including unprotected Remote Desktop Protocol (RDP) configurations, email spam with malicious attachments, deceptive downloads, botnets, exploits, malvertising, web injections, fake updates, and infected installers. The ransomware encrypted a wide range of file types, excluding “.exe” and note text files. The encrypted files were typically found in user folders and temporary directories.
There haven’t been captured pulse or malware samples regarding their purported ongoing operations, Vanderbilt University Medical Center, one of the recent affected entities, issued a statement. A spokesperson for VUMC acknowledged that they were addressing a cyber incident but refrained from disclosing when it took place, whether it involved ransomware, or the extent of the impact resulting from the attack.
Given the evolving tactics of the Meow data extortion team, particularly their shift towards data sales instead of encryption-based ransomware attacks, it’s crucial to adapt mitigation strategies to prioritize data protection. Here’s a comprehensive approach:
Data Classification and Encryption:
Access Control and Least Privilege:
Network Segmentation and Monitoring:
Employee Training and Awareness:
Incident Response Plan:
Backup and Recovery:
Vendor and Third-Party Risk Management:
By implementing these mitigation strategies, organizations can enhance their resilience against data extortion threats posed by groups like Meow, safeguarding sensitive data and minimizing the impact of potential breaches. Regular evaluation and adaptation of these measures are essential to stay ahead of evolving cyber threats.
SOCRadar offers a powerful solution for detecting and mitigating data leaks and credential compromises, safeguarding your business against cyber threats. By continuously monitoring the web, including both surface and dark web sources, SOCRadar swiftly identifies any exposure of sensitive information such as employee emails, customer login details, and credit card numbers.
Use cases of SOCRadar in case of and against a data breach
Moreover, in addition to its many other features, SOCRadar prioritizes critical security incidents, helping your team focus resources where they’re most needed. By ensuring compliance with GDPR regulations and protecting intellectual property, SOCRadar provides comprehensive threat intelligence to fortify your organization’s defenses against data extortion teams like Meow.
Listed below are the TTPs obtained in the analysis of the Meow ransomware strain and their current possible TTPs.
The following are the IoCs for the now decrypted strain of the Meow group; An attack by the new extortion group has not been publicly reviewed.
SHA-256:
SHA-1:
MD5:
Subscribe to our newsletter and stay updated on the latest insights!
PROTECTION OF PERSONAL DATA COOKIE POLICY FOR THE INTERNET SITE
Protecting your personal data is one of the core principles of our organization, SOCRadar, which operates the internet site (www.socradar.com). This Cookie Usage Policy (“Policy”) explains the types of cookies used and the conditions under which they are used to all website visitors and users.
Cookies are small text files stored on your computer or mobile device by the websites you visit.
Cookies are commonly used to provide you with a personalized experience while using a website, enhance the services offered, and improve your overall browsing experience, contributing to ease of use while navigating a website. If you prefer not to use cookies, you can delete or block them through your browser settings. However, please be aware that this may affect your usage of our website. Unless you change your cookie settings in your browser, we will assume that you accept the use of cookies on this site.
1. WHAT KIND OF DATA IS PROCESSED IN COOKIES?
Cookies on websites collect data related to your browsing and usage preferences on the device you use to visit the site, depending on their type. This data includes information about the pages you access, the services and products you explore, your preferred language choice, and other preferences.
2. WHAT ARE COOKIES AND WHAT ARE THEIR PURPOSES?
Cookies are small text files stored on your device or web server by the websites you visit through your browsers. These small text files, containing your preferred language and other settings, help us remember your preferences on your next visit and assist us in making improvements to our services to enhance your experience on the site. This way, you can have a better and more personalized user experience on your next visit.
The main purposes of using cookies on our Internet Site are as follows:
3. TYPES OF COOKIES USED ON OUR INTERNET SITE 3.1. Session Cookies
Session cookies ensure the smooth operation of the internet site during your visit. They are used for purposes such as ensuring the security and continuity of our sites and your visits. Session cookies are temporary cookies and are deleted when you close your browser; they are not permanent.
3.2. Persistent Cookies
These cookies are used to remember your preferences and are stored on your device through browsers. Persistent cookies remain stored on your device even after you close your browser or restart your computer. These cookies are stored in your browser’s subfolders until deleted from your browser’s settings. Some types of persistent cookies can be used to provide personalized recommendations based on your usage purposes.
With persistent cookies, when you revisit our website with the same device, the website checks if a cookie created by our website exists on your device. If so, it is understood that you have visited the site before, and the content to be presented to you is determined accordingly, offering you a better service.
3.3. Mandatory/Technical Cookies
Mandatory cookies are essential for the proper functioning of the visited internet site. The purpose of these cookies is to provide necessary services by ensuring the operation of the site. For example, they allow access to secure sections of the internet site, use of its features, and navigation.
3.4. Analytical Cookies
These cookies gather information about how the website is used, the frequency and number of visits, and show how visitors navigate to the site. The purpose of using these cookies is to improve the operation of the site, increase its performance, and determine general trend directions. They do not contain data that can identify visitors. For example, they show the number of error messages displayed or the most visited pages.
3.5. Functional Cookies
Functional cookies remember the choices made by visitors within the site and recall them during the next visit. The purpose of these cookies is to provide ease of use to visitors. For example, they prevent the need to re-enter the user’s password on each page visited by the site user.
3.6. Targeting/Advertising Cookies
They measure the effectiveness of advertisements shown to visitors and calculate how many times ads are displayed. The purpose of these cookies is to present personalized advertisements to visitors based on their interests.
Similarly, they determine the specific interests of visitors’ navigation and present appropriate content. For example, they prevent the same advertisement from being shown again to the visitor in a short period.
4. HOW TO MANAGE COOKIE PREFERENCES?
To change your preferences regarding the use of cookies, block or delete cookies, you only need to change your browser settings.
Many browsers offer options to accept or reject cookies, only accept certain types of cookies, or receive notifications from the browser when a website requests to store cookies on your device.
Also, it is possible to delete previously saved cookies from your browser.
If you disable or reject cookies, you may need to manually adjust some preferences, and certain features and services on the website may not work properly as we will not be able to recognize and associate with your account. You can change your browser settings by clicking on the relevant link from the table below.
5. EFFECTIVE DATE OF THE INTERNET SITE PRIVACY POLICY
The Internet Site Privacy Policy is dated The effective date of the Policy will be updated if the entire Policy or specific sections are renewed. The Privacy Policy is published on the Organization’s website (www.socradar.com) and made accessible to relevant individuals upon request.
SOCRadar
Address: 651 N Broad St, Suite 205 Middletown, DE 19709 USA
Phone: +1 (571) 249-4598
Email: [email protected]
Website: www.socradar.com
