Threat intelligence enriched with External Attack Surface Management, Brand Protection, and Dark Web Radar.
Protect your business from the dangers lurking in the hidden corners of the internet.
Effective threat hunting and threat actor tracking with behavioral analytics.
Discover your assets with a hacker mindset.
Stay ahead of threat actors with actionable intelligence alerts.
Evaluate the security posture of your entire supply network.
Your guide in harnessing the full potential of our platform.
Hear SOCRadar’s impressive achievements from our clients.
Automate and operationalize your security operations.
Consulting and professional services for cybersecurity excellence.
Industry, sector, and region-based in-depth research.
Discover the heartbeat of cyberspace through a collection showcasing the latest incidents.
Discover how XTI empowers organizations to proactively identify, mitigate, and respond to evolving cyber threats.
Register for our live webinars, and watch our on-demand webinars instantly.
Dive deep into the world of cyber threats, advanced analysis techniques, and cutting-edge strategies.
Stay informed and up-to-date on the latest cybersecurity trends.
Explore SOCRadar’s learning experience to fuel your cybersecurity journey with insights that exceed industry standards.
We offer expert-led, and exclusive trainings to help you master the latest in cybersecurity, trusted by over 2,000 top companies.
Scan the dark web to prevent your leaks from turning into real risks.
Instantly access dark web findings about your organization’s assets.
Check if there is anything about you in SOCRadar’s ever-expanding breach database.
Track threat actors and groups by country or industry for effective follow-up.
Explore threat actors’ tactics, techniques, activities, and detailed profiles targeting your industry or region.
All-in-one next-generation tools for investigating everyday events like phishing, malware, account breach, etc.
Power your search with SOCRadar’s IOC Radar.
Let’s get to know each other better.
Broaden your market reach and increase ARR with SOCRadar Extended Threat Intelligence.
Get informed of our upcoming events.
Latest news about our platform, company, and what’s being said about us.
Begin an extraordinary journey in your professional path with SOCRadar.
We’d like to hear from you.
SOCRadar Training Series – Mastering AI in Cybersecurity From Theory to Practice
Resources
Emerging as a new group in the cybercrime landscape, this Russian-speaking group, WereWolves Ransomware, has gained notoriety recently for its rapid emergence last year. We are going to explore their modus operandi, and their growing list of victims, which stands at 23.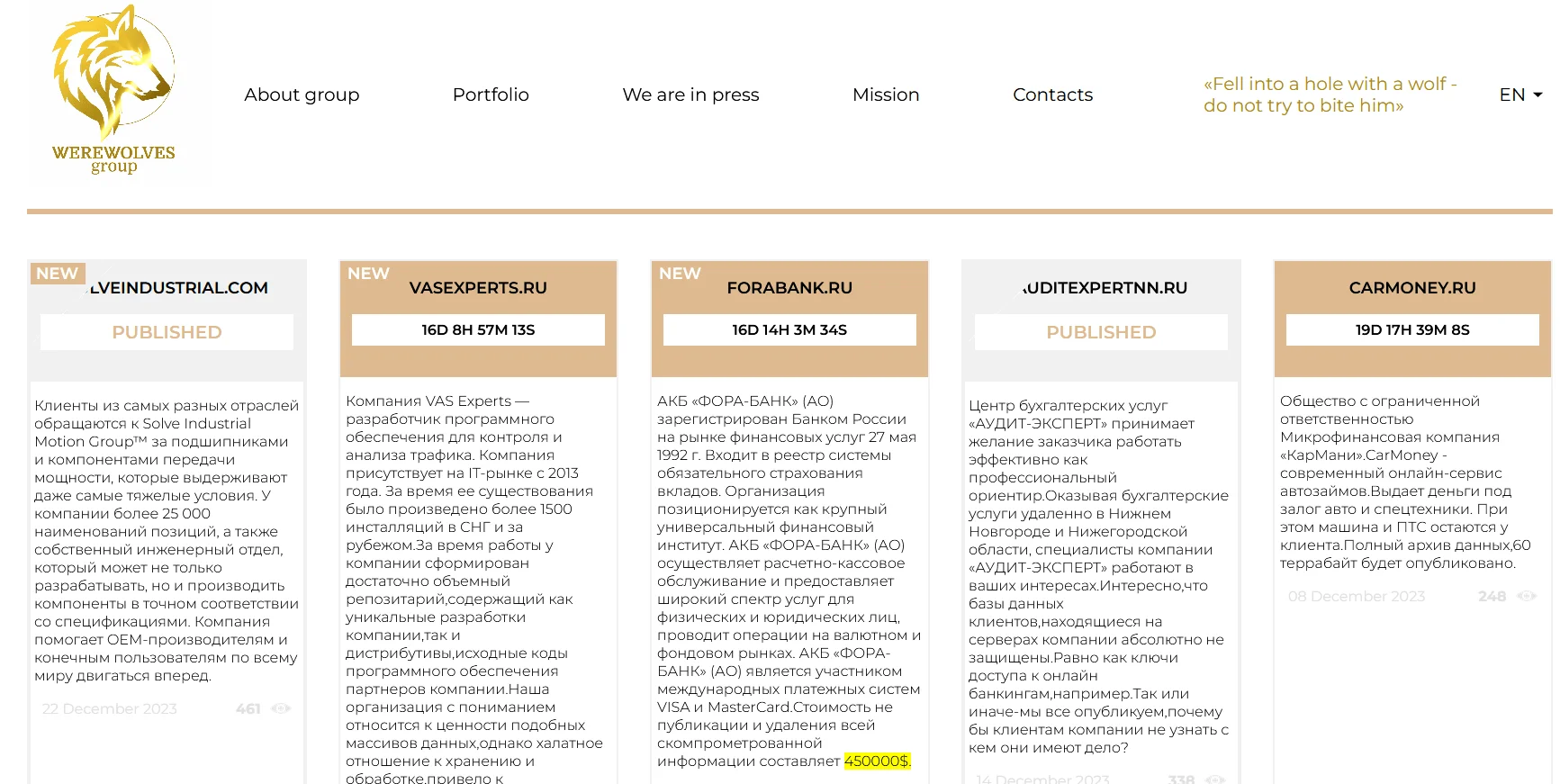
WereWolves’ leak website’s main page
The WereWolves group emerged in May 2023, primarily Russian-speaking, representing a new breed in the cybercrime world. Their communication and operational style reflect their cultural and social origins, offering insights into their methodologies. However, there are still some question marks about the group. The fact that one of their websites has a German name and they list the same victims as LockBit raises a few unanswered questions for now.
WereWolves’ logo on their leak site
The WereWolves ransomware group employs an array of cyber attack techniques, notably seems to be using a variant of the LockBit3 ransomware. Their approach is characterized by double extortion tactics, where they not only encrypt the victim’s data but also threaten to release it publicly unless a ransom is paid. An old version of LockBit was leaked and many threat actors started using different versions, but the situation seems to be different with WereWolves, a possible LockBit affiliate.
Target Demographics
The WereWolves ransomware group’s targeting strategy is diverse, impacting a wide range of industries and businesses globally. Their victims, which have grown to 23 as last checked on January 9, 2024, mostly including mid to small scale enterprises and organizations, indicating a preference for easy targets. However, it does not appear that they are focusing on a specific country for now, which may indicate that they have a purely financial motivation.
Recruitment Strategies
The recruitment strategies of the WereWolves group are as intriguing as their cyber attacks. Unlike many cybercrime groups that operate in secrecy, the WereWolves have taken a more open and humorous approach to expanding their team.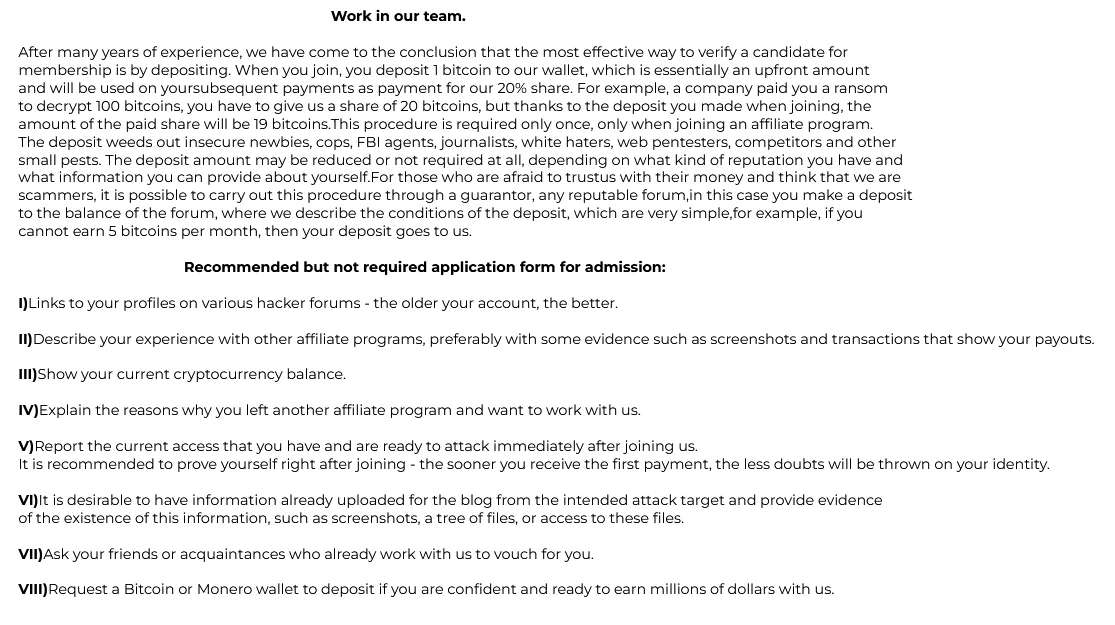
They have a “Work in our team.” section on their victim sharing website
Online Presence and Communication
The WereWolves ransomware group distinguishes itself with an engaging online presence. Their operational website is more than just a platform for communication; it serves as a hub for propaganda, information dissemination, and recruitment. They utilize their online presence to further their goals, interact with their victims, and maintain their cybercriminal network. This aspect of their operation highlights the modern ways in which cybercrime groups adapt to and leverage the digital landscape for their nefarious activities.
On their Mission page, they say that they provide a pentest service, which is a classic ransomware group joke that is not very original.
Affiliations and Comparisons
An interesting observation from HackManac’s blog post is that six of the victims listed by the WereWolves group seem to be identical to those previously targeted by the LockBit group. These include various organizations like the Agency for Electronic Communications and La Poste Mobile. The postings about these victims show striking similarities, including identical samples and the same amount of data claimed to be exfiltrated. This raises questions about the overlap or potential connections between these two cybercrime entities.
The WereWolves ransomware group, characterized by their Russian-speaking origins, has targeted a range of sectors from Finance to Manufacturing. Their approach is looking random but they seem to focus on easy to attack but have high impact industries like small to mid scale services and organizations. This could also make their operations not just financially motivated but also potentially disruptive on a larger scale.
The group’s selection of targets underlines their intent to cause significant operational and financial distress to extract ransomware, impacting sectors that are crucial to the functioning of various economies and societies.
However, unlike traditional Russian ransomware groups, both Russian and former Soviet countries or countries close to the Soviets are included in their victim lists.
On their leak website, 4th of the 5 victim has .ru domain
The WereWolves group has an authentic approach, but there are doubts about their attacks. As HackManac stated well, verifying or disproving WereWolves’ cyber attacks is crucial for understanding the real threat this ransomware group presents, especially as they’ve largely operated unnoticed. The occurrence of six attacks simultaneously with LockBit’s activities raises the possibility of a connection between these two cybercriminal groups. Ongoing vigilance and monitoring are essential to fully grasp WereWolves’ operations and intentions.
Considering that even a minor incident may lead to further cyber attacks, this one year old group utilizing a dangerous LockBit Black variant underscores the need for vigilant, adaptive cyber defenses to mitigate such threats.
Subscribe to our newsletter and stay updated on the latest insights!
PROTECTION OF PERSONAL DATA COOKIE POLICY FOR THE INTERNET SITE
Protecting your personal data is one of the core principles of our organization, SOCRadar, which operates the internet site (www.socradar.com). This Cookie Usage Policy (“Policy”) explains the types of cookies used and the conditions under which they are used to all website visitors and users.
Cookies are small text files stored on your computer or mobile device by the websites you visit.
Cookies are commonly used to provide you with a personalized experience while using a website, enhance the services offered, and improve your overall browsing experience, contributing to ease of use while navigating a website. If you prefer not to use cookies, you can delete or block them through your browser settings. However, please be aware that this may affect your usage of our website. Unless you change your cookie settings in your browser, we will assume that you accept the use of cookies on this site.
1. WHAT KIND OF DATA IS PROCESSED IN COOKIES?
Cookies on websites collect data related to your browsing and usage preferences on the device you use to visit the site, depending on their type. This data includes information about the pages you access, the services and products you explore, your preferred language choice, and other preferences.
2. WHAT ARE COOKIES AND WHAT ARE THEIR PURPOSES?
Cookies are small text files stored on your device or web server by the websites you visit through your browsers. These small text files, containing your preferred language and other settings, help us remember your preferences on your next visit and assist us in making improvements to our services to enhance your experience on the site. This way, you can have a better and more personalized user experience on your next visit.
The main purposes of using cookies on our Internet Site are as follows:
3. TYPES OF COOKIES USED ON OUR INTERNET SITE 3.1. Session Cookies
Session cookies ensure the smooth operation of the internet site during your visit. They are used for purposes such as ensuring the security and continuity of our sites and your visits. Session cookies are temporary cookies and are deleted when you close your browser; they are not permanent.
3.2. Persistent Cookies
These cookies are used to remember your preferences and are stored on your device through browsers. Persistent cookies remain stored on your device even after you close your browser or restart your computer. These cookies are stored in your browser’s subfolders until deleted from your browser’s settings. Some types of persistent cookies can be used to provide personalized recommendations based on your usage purposes.
With persistent cookies, when you revisit our website with the same device, the website checks if a cookie created by our website exists on your device. If so, it is understood that you have visited the site before, and the content to be presented to you is determined accordingly, offering you a better service.
3.3. Mandatory/Technical Cookies
Mandatory cookies are essential for the proper functioning of the visited internet site. The purpose of these cookies is to provide necessary services by ensuring the operation of the site. For example, they allow access to secure sections of the internet site, use of its features, and navigation.
3.4. Analytical Cookies
These cookies gather information about how the website is used, the frequency and number of visits, and show how visitors navigate to the site. The purpose of using these cookies is to improve the operation of the site, increase its performance, and determine general trend directions. They do not contain data that can identify visitors. For example, they show the number of error messages displayed or the most visited pages.
3.5. Functional Cookies
Functional cookies remember the choices made by visitors within the site and recall them during the next visit. The purpose of these cookies is to provide ease of use to visitors. For example, they prevent the need to re-enter the user’s password on each page visited by the site user.
3.6. Targeting/Advertising Cookies
They measure the effectiveness of advertisements shown to visitors and calculate how many times ads are displayed. The purpose of these cookies is to present personalized advertisements to visitors based on their interests.
Similarly, they determine the specific interests of visitors’ navigation and present appropriate content. For example, they prevent the same advertisement from being shown again to the visitor in a short period.
4. HOW TO MANAGE COOKIE PREFERENCES?
To change your preferences regarding the use of cookies, block or delete cookies, you only need to change your browser settings.
Many browsers offer options to accept or reject cookies, only accept certain types of cookies, or receive notifications from the browser when a website requests to store cookies on your device.
Also, it is possible to delete previously saved cookies from your browser.
If you disable or reject cookies, you may need to manually adjust some preferences, and certain features and services on the website may not work properly as we will not be able to recognize and associate with your account. You can change your browser settings by clicking on the relevant link from the table below.
5. EFFECTIVE DATE OF THE INTERNET SITE PRIVACY POLICY
The Internet Site Privacy Policy is dated The effective date of the Policy will be updated if the entire Policy or specific sections are renewed. The Privacy Policy is published on the Organization’s website (www.socradar.com) and made accessible to relevant individuals upon request.
SOCRadar
Address: 651 N Broad St, Suite 205 Middletown, DE 19709 USA
Phone: +1 (571) 249-4598
Email: [email protected]
Website: www.socradar.com
